Dark Web Links Collection 2022 Working Tor Sites Links
Dark Web Links Directories And Hidden Wiki Link
DarkWeb.Link brings you the latest Dark Web Links, bookmark the site in Tor browser as your personal front page to the dark web. Here we have brought to you a list of dark web links as well as dark web sites from the hidden dark web world. Hope you will enjoy getting all dark web links in one place. We have dug out these dark web sites from the dark web which is unknown to most of the online surfer.
One of the oldest Hidden Wikis can be found here:
http://jaz45aabn5vkemy4jkg4mi4syheisqn2wn2n4fsuitpccdackjwxplad.onion/ OnionLinks v3
http://xsglq2kdl72b2wmtn5b2b7lodjmemnmcct37owlz5inrhzvyfdnryqid.onion/ The Hidden Wiki
http://bj5hp4onm4tvpdb5rzf4zsbwoons67jnastvuxefe4s3v7kupjhgh6qd.onion/ Another Hidden Wiki
http://qrtitjevs5nxq6jvrnrjyz5dasi3nbzx24mzmfxnuk2dnzhpphcmgoyd.onion/ Pug’s Ultimate Dark Web Guide
Dark Web Drug Vendors

If you are a regular user of the internet and are looking to buy some Dark Web drugs, then you are at the right place. A well-known website list is given below to find your perfect dark web drug vendors:
http://wms5y25kttgihs4rt2sifsbwsjqjrx3vtc42tsu2obksqkj7y666fgid.onion/ DCdutchconnectionUK – The dutch connection for the UK
http://gkcns4d3453llqjrksxdijfmmdjpqsykt6misgojxlhsnpivtl3uwhqd.onion/ DrChronic – Weed straight from the source
http://c5xoy22aadb2rqgw3jh2m2irmu563evukqqddu5zjandunaimzaye5id.onion/ TomAndJerry – Cocaine, Heroin, MDMA and LSD from NL
http://rbcxodz4socx3rupvmhan2d7pvik4dpqmf4kexz6acyxbucf36a6ggid.onion/ 420prime – Cannabis in dispensary quality from the UK
http://7bw24ll47y7aohhkrfdq2wydg3zvuecvjo63muycjzlbaqlihuogqvyd.onion/ Bitpharma – Biggest european .onion drug store
http://wges3aohuplu6he5tv4pn7sg2qaummlokimim6oaauqo2l7lbx4ufyyd.onion/ EuCanna – First Class Cannabis
http://porf65zpwy2yo4sjvynrl4eylj27ibrmo5s2bozrhffie63c7cxqawid.onion/ Smokeables – Finest organic cannabis from the USA
http://hyxme2arc5jnevzlou547w2aaxubjm7mxhbhtk73boiwjxewawmrz6qd.onion/ CannabisUK – UK wholesale cannabis supplier
http://6hzbfxpnsdo4bkplp5uojidkibswevsz3cfpdynih3qvfr24t5qlkcyd.onion/ Brainmagic – Best Darkweb psychedelics
http://gn74rz534aeyfxqf33hqg6iuspizulmvpd7zoyz7ybjq4jo3whkykryd.onion/ NLGrowers – Coffee Shop grade Cannabis from the Netherlands
http://4p6i33oqj6wgvzgzczyqlueav3tz456rdu632xzyxbnhq4gpsriirtqd.onion/ Peoples Drug Store – The Darkwebs best Drug supplier!
http://dumlq77rikgevyimsj6e2cwfsueo7ooynno2rrvwmppngmntboe2hbyd.onion/ DeDope – German Weed Store
Dark Web Wallets And Bitcoin Mixers
http://cr32aykujaxqkfqyrjvt7lxovnadpgmghtb3y4g6jmx6oomr572kbuqd.onion/ Dark Mixer – Anonymous bitcoin mixer
http://74ck36pbaxz7ra6n7v5pbpm5n2tsdaiy4f6p775qvjmowxged65n3cid.onion/ Mixabit – Bitcoin mixer
http://vu3miq3vhxljfclehmvy7ezclvsb3vksmug5vuivbpw4zovyszbemvqd.onion/ EasyCoin – Bitcoin Wallet and Mixer
http://zwf5i7hiwmffq2bl7euedg6y5ydzze3ljiyrjmm7o42vhe7ni56fm7qd.onion/ Onionwallet – Anonymous and secure bitcoin wallet and mixer
http://5kpq325ecpcncl4o2xksvaso5tuydwj2kuqmpgtmu3vzfxkpiwsqpfid.onion/ VirginBitcoins – Buy freshly mined clean bitcoins
Other Tor Market Sites
http://zkj7mzglnrbvu3elepazau7ol26cmq7acryvsqxvh4sreoydhzin7zid.onion/ Dark Web Hackers for hire
http://z7s2w5vruxbp2wzts3snxs24yggbtdcdj5kp2f6z5gimouyh3wiaf7id.onion/ AccMarket – Premium Paypal, Ebay and bank accounts
http://f6wqhy6ii7metm45m4mg6yg76yytik5kxe6h7sestyvm6gnlcw3n4qad.onion/ Cardshop – USA CVV KNOWN BALANCE & Worldwide CC & CVV
http://sazyr2ntihjqpjtruxbn2z7kingj6hfgysiy5lzgo2aqduqpa3gfgmyd.onion/ Darkmining – Bitcoin mining with stolen electricity
http://2ezyofc26j73hv3xxvsrnbc23dqxhgxqtk5ogcc7y6j5t6rlqquvhzid.onion/ Bitcoin Investment Trust – earn 5-9% per week!
http://ez37hmhem2gh3ixctfeaqn7kylal2vyjqsedkzhu4ebkcgikrigr5gid.onion/ Mobile Store – Best unlocked cell phones vendor
http://bepig5bcjdhtlwpgeh3w42hffftcqmg7b77vzu7ponty52kiey5ec4ad.onion/ Kamagra 4 Bitcoin – Like Viagra but cheaper
http://endtovmbc5vokdpnxrhajcwgkfbkfz4wbyhbj6ueisai4prtvencheyd.onion/ OnionIdentityServices – Fake passports and ID cards for bitcoin
http://onili244aue7jkvzn2bgaszcb7nznkpyihdhh7evflp3iskfq7vhlzid.onion/ Uk Guns and Ammo Store
http://7wsvq2aw5ypduujgcn2zauq7sor2kqrqidguwwtersivfa6xcmdtaayd.onion/ USfakeIDs – US fake ID store
http://pliy7tiq6jf77gkg2sezlx7ljynkysxq6ptmfbfcdyrvihp7i6imyyqd.onion/ Counterfeit USD – High Quality USD counterfeits
http://pz5uprzhnzeotviraa2fogkua5nlnmu75pbnnqu4fnwgfffldwxog7ad.onion/ USAcitizenship – become a citizen of the USA
http://hyjgsnkanan2wsrksd53na4xigtxhlz57estwqtptzhpa53rxz53pqad.onion/ EuroGuns
http://awsvrc7occzj2yeyqevyrw7ji5ejuyofhfomidhh5qnuxpvwsucno7id.onion/ Apples4Bitcoin – Iphones, Ipads and more for bitcoin
http://wosc4noitfscyywccasl3c4yu3lftpl2adxuvprp6sbg4fud6mkrwqqd.onion/ UKpassports – real UK passports
http://gch3dyxo5zuqbrrtd64zlvzwxden4jkikyqk3ikjhggqzoxixcmq2fid.onion/ ccPal – PayPals, Ebays, CCs and more
http://jn6weomv6klvnwdwcgu55miabpwklsmmyaf5qrkt4miif4shrqmvdhqd.onion/ Rent-A-Hacker – Hire a hacker for Bitcoin
http://2bcbla34hrkp6shb4myzb2wntl2fxdbrroc2t4t7c3shckvhvk4fw6qd.onion/ Webuybitcoins – Sell your Bitcoins for Cash, Paypal, WU etc
http://sa3ut5u4qdw7yiunpdieypzsrdylhbtafyhymd75syjcn46yb5ulttid.onion/ HQER – High Quality Euro bill counterfeits
All Other Sites
http://danielas3rtn54uwmofdo3x2bsdifr47huasnmbgqzfrec5ubupvtpid.onion/ DanielWin
http://answerszuvs3gg2l64e6hmnryudl5zgrmwm3vh65hzszdghblddvfiqd.onion/ Hidden Answers
https://kcmykvkkt3umiyx4xouu3sjo6odz3rolqphy2i2bbdan33g3zrjfjgqd.onion/ aboutMastodon
http://dhosting4xxoydyaivckq7tsmtgi4wfs3flpeyitekkmqwu4v4r46syd.onion/ Daniels Hosting
http://cathug2kyi4ilneggumrenayhuhsvrgn6qv2y47bgeet42iivkpynqad.onion/ cathugger’s site
http://zgeajoabenj2nac6k5cei5qy62iu5yun5gm2vjnxy65r3p3amzykwxqd.onion/ Darkweb Blog
http://ozmh2zkwx5cjuzopui64csb5ertcooi5vya6c2gm4e3vcvf2c2qvjiyd.onion/ riseup searx
http://45tbhx5prlejzjgn36nqaxqb6qnm73pbohuvqkpxz2zowh57bxqawkid.onion/ Parckwart’s Website
http://sidignlwz2odjhgcfhbueinmr23v5bubq2x43dskcebh5sbd2qrxtkid.onion/ securejabber
http://sik5nlgfc5qylnnsr57qrbm64zbdx6t4lreyhpon3ychmxmiem7tioad.onion/ Qubes OS
http://dds6qkxpwdeubwucdiaord2xgbbeyds25rbsgr73tbfpqpt4a6vjwsyd.onion/ Whonix
http://lldan5gahapx5k7iafb3s4ikijc4ni7gx5iywdflkba5y2ezyg6sjgyd.onion/ OnionShare
http://nanochanqzaytwlydykbg5nxkgyjxk3zsrctxuoxdmbx5jbh2ydyprid.onion/ NanoChan
http://picochanwvqfa2xsrfzlul4x4aqtog2eljll5qnj5iagpbhx2vmfqnid.onion/ PicoChan
http://enxx3byspwsdo446jujc52ucy2pf5urdbhqw3kbsfhlfjwmbpj5smdad.onion/ EndChan
http://dngtk6iydmpokbyyk3irqznceft3hze6q6rasrqlz46v7pq4klxnl4yd.onion/ 256Chan
http://cct5wy6mzgmft24xzw6zeaf55aaqmo6324gjlsghdhbiw5gdaaf4pkad.onion/ Snopyta
http://wnrgozz3bmm33em4aln3lrbewf3ikxj7fwglqgla2tpdji4znjp7viqd.onion/ VYempire.xyz
http://7sk2kov2xwx6cbc32phynrifegg6pklmzs7luwcggtzrnlsolxxuyfyd.onion/ SystemLI.org
http://stormwayszuh4juycoy4kwoww5gvcu2c4tdtpkup667pdwe4qenzwayd.onion/ CryptoStorm VPN
http://xdkriz6cn2avvcr2vks5lvvtmfojz2ohjzj4fhyuka55mvljeso2ztqd.onion/ Cock.li
http://eludemailxhnqzfmxehy3bk5guyhlxbunfyhkcksv4gvx6d3wcf6smad.onion/ Elude.in
http://lainwir3s4y5r7mqm3kurzpljyf77vty2hrrfkps6wm4nnnqzest4lqd.onion/ qord11.net
http://cgjzkysxa4ru5rhrtr6rafckhexbisbtxwg2fg743cjumioysmirhdad.onion/ Course Enigma
http://killnod2s77o3axkktdu52aqmmy4acisz2gicbhjm4xbvxa2zfftteyd.onion/ Kill9
http://digdeep4orxw6psc33yxa2dgmuycj74zi6334xhxjlgppw6odvkzkiad.onion/ DigDeeper
http://spywaredrcdg5krvjnukp3vbdwiqcv3zwbrcg6qh27kiwecm4qyfphid.onion/ Spyware Watchdog
http://meynethaffeecapsvfphrcnfrx44w2nskgls2juwitibvqctk2plvhqd.onion/ May Vane Day Studios
http://zsxjtsgzborzdllyp64c6pwnjz5eic76bsksbxzqefzogwcydnkjy3yd.onion/ Shadow Wiki
http://g7ejphhubv5idbbu3hb3wawrs5adw7tkx7yjabnf65xtzztgg4hcsqqd.onion/ Defcon
http://p53lf57qovyuvwsc6xnrppyply3vtqm7l6pcobkmyqsiofyeznfu5uqd.onion/ Propublica
http://darkzzx4avcsuofgfez5zq75cqc4mprjvfqywo45dfcaxrwqg6qrlfid.onion/ Darknetlive
http://keybase5wmilwokqirssclfnsqrjdsi7jdir5wy7y7iu3tanwmtp6oid.onion/ KeyBase.IO
http://ciadotgov4sjwlzihbbgxnqg3xiyrg7so2r2o3lt5wz5ypk4sxyjstad.onion/ CIA.GOV
http://archivebyd3rzt3ehjpm4c3bjkyxv3hjleiytnvxcn7x32psn2kxcuid.onion/ Internet Archive
http://bible4u2lvhacg4b3to2e2veqpwmrc2c3tjf2wuuqiz332vlwmr4xbad.onion/ Bible4u
http://kx5thpx2olielkihfyo4jgjqfb7zx7wxr3sd4xzt26ochei4m6f7tayd.onion/ Imperial Library
http://nv3x2jozywh63fkohn5mwp2d73vasusjixn3im3ueof52fmbjsigw6ad.onion/ Comic Books
What Are Dark Web Links?

Dark Web Links are .onion domains on the Tor network, .onion domains are hosted as a Tor hidden service.
You can browse to Dark Web Links with the Torbrowser, or Onion Browser on the Iphone.
So if you are wondering how to access the dark web, all you need is the links on this site and a dark web browser.
There are the old style .onion hidden service links, and now also the new version 3 links which are much longer. But both are working the same way.
Just browse to DarkWeb.Link with your Torbrowser to access the dark web. And check our Blog for more articles about dark web sites and their links.
When did the Dark Web “start”?
The history of the anonymous web is almost as old as the present history of the Internet. We did not find any official record of the actual “start date”, but we believe that the Dark Web that we know today began with the release of Free net in 2000 .
Download and Install Tor Browser
Despite its current use as a browser that is often used to access parts of the Dark Web, TOR (aka. Dark web browser) was originally developed to help protect US intelligence online communications .
Today, this witch is one of the few ways to access onion websites located on the web.
TOR is a modern version of the famous Firefox web browser, wisely modified to allow users to browse the web world anonymously. Browsers are designed to block or advise user efforts to do things that may reveal their identity, such as resizing the dimensions of a browser window, for example.
Please click here to download Tor Browser.
DARK WEB: – A COMPREHENSIVE ARTICLE ON HOW TO USE
Dark web has been a fascinating little entertainment for multitudes. The way it protected a class of people will surely attract masses. The wordings dark web and Tor have been interchanged in many fields. Weill, this article will be an eye opener on who benefits from TOR. Numerous infamous incidents have tarnished the glamorous outfit of black web. However, no matter how hard authorities try to defame it, the interesting aspect of dark web will always captivate it. Dark web doesn’t facilitate any crime. TOR volunteers have been supportive to any assistance required for solving criminal cases. The unearthing of Silk Road was an example. During recent conventions, the authorities have made it clear that TOR networks facilitate only anonymous traffic and nothing more. It is the user who shall be held captive for wrong doings. The ease of doing business in TOR has certainly allured many criminals to it. Be it services or delivery of banned goods, TOR assists them due to its privacy first attitude. Also, the advancement of cryptocurrencies has also boosted activities.
TRACKING ACTIVITIES IN DARK WEB

The introduction of better tools and sophisticated techniques has assisted law enforcement agencies. It is possible to analyze packets and end users with time and effort. Even after repeated attempts to bring down several child pornographies sites, there has been little luck. The lack of advancement is due to much better tricks that marketplaces opt to evade themselves. Now, it is even harder to track any malicious activities. But thanks to progression in technology, the same is made possible. Last year, few attempts to bring down marketplaces selling illegal goods were successful. TOR has been in the comfort zone for many years now. But the future of TOR is unpredictable. Whether it is about a new technology promising more anonymity or it’s just a revamp, we have to wait and see. TOR, as of now has a strong user base even though it has only 3 percent of market share. Furthermore, events leading to disgraceful incidents are also on the rise in TOR. Lately, federal authorities are tracing more and more e-commerce platforms in the dark net. If the situation continues, more sellers will be forced to leave TOR networks. Dark web links are also unstable as of now.
WHY USERS OPT FOR DARK WEB SERVICES

As an investigator or a casual user with investigative mind, what makes a person allured into dark web? The answer has a choice from a wide spectrum. It isn’t anyone’s choice to always opt for dark web. Some of them do it with an intention to purchase illicit goods. Some sell items and benefit from anonymity. Some are there to just take a glance of what exactly is happening. Most important of all, there are the web administrators. Websites that are up and running cannot carry out all tasks automatically. There has to be a point where manual intervention is required. Here comes the real culprit. It cannot be construed as an excellent option to hide beneath TOR networks. Illicit trade has boomed over the past few times. Again, all the web links available in dark web aren’t illegal. Interesting web pages coupled with tons of entertaining social media sites are also available. The question again is, then why does dark web feel so dark? For an answer, we will have to drive back areas.
DARK WEB FROM THE BEGINNING

Dark web was young when it surfaced as a measure to contain eavesdropping and to finally secure data. The Naval Research Laboratory funded by the US developed TOR network, what is lovingly termed as dark web nowadays. The achievement was sort of rebellious with no other alternative for internet back then. Later, several changes came to the tor project and it was publicly supported not as a governmental project but as a common one. One of the main aims off pushing such a project to existence was to secure data. Information was vital and any steps to prevent siphoning it were termed awesome. Then came the advent of advanced technical developments. Dark web found it hard to sustain itself from the very small funds. The project had a small but like-minded volunteer group compared to surface web. Websites started to grow and evolve. User groups were also enjoying the various .onion extensions they had. During the leaning phase, somewhere, the purpose of tor was overlooked. Dark web marketplaces hosting illegal content and illicit trades became regular. The rest is history.
AN UNDERSTANDING OF DIFFERENCE BETWEEN DARK WEB AND SURFACE WEB
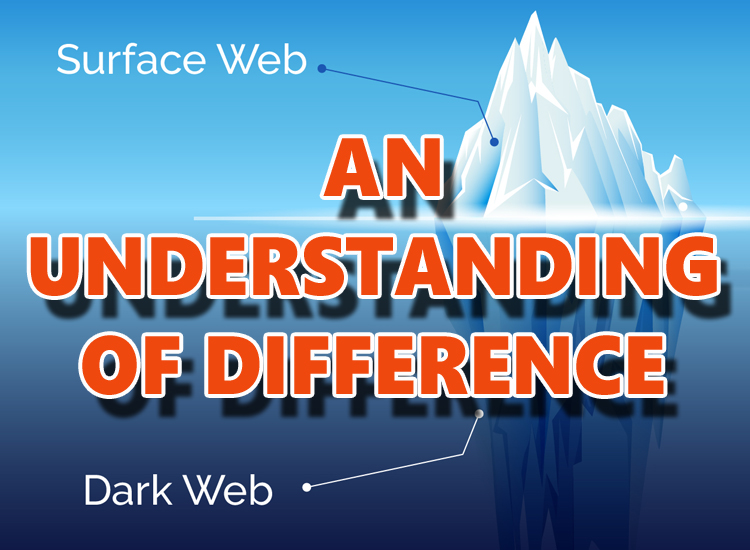
It is better to have a brief understanding of its operation and terminology before you jump into conclusion on what exactly the dark web offers. Over the historical eras, the dark web has advanced, cheering for an extensive operator base. In the minds of netizens, crazy tales about services accessible through dark web links have generated suspicion. Facilities here are said to be available, including that of a hitman. In one step, for illustration, the site called Besa Mafia had its being. But instead of offering a hitman’s services as promised, the site was a mere phishing attempt on its users’ personal details and financial assets. Surface web has more content that can be tracked. This assists enforcement authorities to have a clear picture. Dark web on the other hand is a maze of criminal activities. It is hard to track and much harder to convict anyone makes it a safe haven. That is what dark web is.
TIPS TO STAY SAFE IN DARK WEB

For several years now, Tor has been in the limelight. There has been widespread applause for the simple and free use of the layout. It should be agreed that the glitz of new gen clear net counterparts is absent from dark web pages. But when it comes to performance, it is difficult to put the dark web aside. Among investigation agencies, websites hosting dark content are infamous. As such, TOR networks constitute a viable means of transporting malicious goods. The negative side of it also conceals the positive aspect of dark net operations. A customer who is able to differentiate the good and the poor and categorize them will have a good time using their services.
NETWORKING AND DARK WEB

The divergence in networked systems has made it simpler for hackers to spread infections than ever. In the dark web links, malware of varying size and infection rate is now available. This article provides some of the resources provided by the Dark web. It is recommended that net users avoid such websites because they bear infections and most likely you will not receive the requested service. Infections or similar attacks in the dark marketplaces are popular. There is denial that can be introduced to service bots. Worms of the new generation requires no installation experience and it is a simple click to install the kit. Trojans with RAT or Remote Access are also valuable resources for hackers. Dark web systems comprise of a TOR enabled browser and many relayed nodes. These nodes carry data to various parts of the system. The relayed network system makes it harder to track and bring down Dark web markets.
ENFORCING LAWS ON DARK WEB

There isn’t a single mechanism with which the atrocities can be limited. TOR itself is vast and the basic technology hinders any identification. Newer methodologies coupled with prompt penalties have suppressed marketplace owners. However, dark web is growing. Ups and downs of dark web were time tested and still the whole system is evolving. Newer domains will surely replace existing concepts to bring dark web live. The current scenario is that security in dark web is purely the visitor’s bane. There is no pre written script to save you. If known facts will save someone from enforcement authorities then one useful tip is to stay away from illegal markets. You will almost always end up in hand cuffs. A steel stomach may not always save a dark web user from the wrath of scammers. Plenty of excuses can be found to access dark web. Whatever demanding the situation is, it is always a risk to skim the pages of dark net.
ACCESSING DARK WEB SITES

Companies who have lately found that their data is compromised and available in the dark web need to act immediately. Time should not be wasted. An in-depth flush of the notorious dark space is inevitable. But, how to and when to access, it is the main question. With the proper tools onboard, this article will surely hint you on how to safely move ahead. Corporate information is selling like hot cakes. The only way to stop it is to update network security. However, most of the timers, data is spilled over the roof by employees itself. This cannot be treated alone. Thus, monitoring the dark web requires important. Simply surfing the dark web isn’t enough for finding stashed data. Logging into accounts and creating user ids is required at times. A veteran network administrator can surely assist in such activities. Dark web portals required to be search thoroughly for stolen data. Individuals may make use of the social media as well as online forums to identify data thefts. Most of the social media websites have their dark web counterpart up and functional.
PLANNING AFTER DATA BREACH IN DARK WEB SITES

Some of the other offerings available on dark web links are login data, bank records and stolen credit cards. While some of the websites are outdated and not running, there are few markets that flourish with operation. Therefore, it is necessary to protect your computer and prevent unauthorized access to it using security tools. When compromised, the data will land in this area very well. Anyone with a balance of cryptocurrencies may easily purchase this knowledge and enjoy the advantages. Therefore, it is important to have VPN installed. Choosing a VPN is as simple as choosing a VPN service and paying for the most appropriate plan. It’s a breeze to install a service. One such VPN service that delivers excellent after-sales support is NordVPN. At the same time, it safeguards different devices. The platform-independent VPN offers incredible standards of encryption. A VPN helps to anonymize the transfer of data that happens on networks. VPN services provide users with different levels of experience with their helping hands. They also allow Deep Web for safe surfing, and web of the surface and dark web. Some might consider it a silly idea to invest in a VPN.
DARK WEB SITES AND ORGANIZATIONAL IMPACT

Setting and finalizing a goal is the first thing to focus on once your organization’s data has been compromised. The lack of manpower or mistrust in data admins is not to be complained for. Individuals should focus on email communication and encrypted forms of data. Dark web sites carry all sorts of threats to clients. Once any relevant information is received, TOR access can be easily shut and the data thus saved can be removed for future purpose. During the uptime in TOR, personal data should not be shared anywhere. There shouldn’t be any active instances of JavaScript activation as well. Once a data breach has occurred, there isn’t much time for a backup. Solutions should be prompt and spot on. Without a doubt, the plan of disconnecting network computers should be processed. There shouldn’t be any delay in sanitizing computers using antivirus software. Updated software is also an important aspect of security. The programs installed should be monitored and renewed as and when required.
INSTALLATION AND SETTING UP TOR FOR DARK WEB LINKS

Dark web is a little fantasy for young users. The merry land of dull websites is what some term dark net as. But that is not all. Dark web has evolved into a mixed list of surprises. The old man who surfs dark web will surely experience his teenage there with dull plain html pages loading forever. The experience thus provided may not be pleasing for all. Installation is pretty simple and straightforward. TOR networks are backed up by powerful relay networks. Thus, first of all, users need to install tor enabled browsers. Dark web links are accessible only through a compatible browser. These can be downloaded from the internet. TOR browser is a very good online browser with loads of features. It assists in completing dark web related searches. TOR browsers have in built onion routing capability. One of the essential features for a tor browser is privacy. Search Engines related to dark web links searches provide this facility. One of the available features also includes privacy.
TOR SERVICES AND ANONYMITY OF DARK WEB
Wonderful it may seem, TOR guarantees anonymity. Dark web is a mesmerizing piece of puzzle which piles up every known atrocity in the internet. This does not mean dark web facilitates it. The word dark is often misused in this context. Dark web is a wonderful place for anonymous users to gather and express concerns. Dark web links and associated dark web activities have been in the internet for a long time. Mysterious activities take place at this depth of World Wide Web. Hard to trace and hard to reach are attributes while using dark web. As the common stereotype may refer to dark web for illegal activities, the trust is not that confirmed. How and what is dark web will give internet citizens a bit clearer view of the happening. To start off, the internet is a conglomeration of many million servers, clients, routers and other network garbage. Both soft3ware and hardware work in tandem to achieve efficiency in user searches. The software part comprises of browsers and programs that control routers. Dark web is facilitated by relays. A relay refers to a group of clients or computers. They are spread all over the internet.
DEEPER ON DARK WEB
The chunk of ice berg is dark web. This is meaningful when surface web is compared to tip of the ice berg. A user who got the gist of dark web is an advanced net user. A good amount of traffic occurs in block space of internet through Dark web links. It is also common for dark net users to be on multiple platforms at same time. With just over .01 percent of market share, dark web links isn’t to be blamed. Well, illegal activities occur in all troves of internet. But unlike surface web, tor networks aim to preserve privacy. This mode of anonymity makes fighting hard for enforcement authorities. Dark web is often perplexing in behavior. Marketplaces are among the most notorious in dark net. The markets host whatever illicit goods you can find in real world. No, that hitman service will surely land you in jail if that is your question of importance. Double check whether shared ports, hardware acceleration and serial port connectivity are switched off by default before turning off the Virtual Machine. These options offer malicious attackers a hint about the details of your computer.
GOVERNMENTS AND DARK WEB

The regulation of internet laws and corresponding censorship were topics of debate during the past few years. Technical advancement has really concerned governments. There are wireless portals where dark web is free to explore. We live in a complex world with much technical know-how still confusing for the masses. The laws are ever changing and dark web seems to violate the basic laws at times. Enacting strict policies will surely bring more discipline to internet. Dark web is a relevant portion of internet. It needs studies and researches before banning a service. Also, certain countries have more versatile laws for internet freedom. Some have been rigid causing uprisings and concerns. Dark web cannot be blasted all of a sudden. Tracking servers and bringing them down requires patience and support of relays of dark web itself. Presently the laws of many developed countries are not adequate to track and bring illegal websites down. Therefore, it is inevitable to discipline the laws regulating internet usage first. Dark web markets aid in boosting banned drug sale also. Stringent measures including prison terms need to be imposed to bring such activities down.
GOVERNMENTAL POLICIES ON TACKLING DARK WEB
Dark web interconnects users with services available in TOR network. The principle of anonymity and increased security makes this possible. Users can conceal their identity online and make them safe before publishing required data. Dark web is spread all over the world. It has roots in most of the continents. Even officials of government organizations rely on dark web for disseminating information safely. The entry of internet groups involved in various countries have brought forward requirement of new laws. The present scenario is complicated. The laws need to be enacted in such a way that a dark web user in another country needs to avail the protection. Actions that are prohibited by law in a country will be allowed in another. Thus, regulating international actions need to have a common consensus. This requires framing of international laws for regulating internet freedom. The scope of this work is complex and beyond comparison due to freedom that citizens of few countries enjoy.
USEFUL LINKS IN DARK WEB

Although not as common as the famed surface web, dark web also has its own quiver of arrows for entertaining users. The darker shade of dark web may not be pleasing for all audience. Hence, it is suggested to stick with healthy browsing practices. Before going in depth on topics related to dark web, a word of caution for all users of the dark network. It is highly recommended to use a VPN. VPN is not a mere security layer; it is a lifesaving mechanism there days. With all the ransomwares floating around, it is hard to save someone with dark web security alone. VPN solves this problem. VPN adds another layer of robust security anonymizing the user and his connected device. This article contains few useful links with a brief description of websites that may be useful while browsing TOR networks.
TOOLS FOR DARK WEB SITE ACCESS

Surfshark is a useful tool available for a few dollars on a monthly subscription basis. Surfshark does what it advertises the best; internet data encryption. Data privacy is guarded by installation of this tool. Scammers and hackers will have a hard time accessing your private data. Their updated testing mechanism also tracks any outgoing traffic as well. Surfshark also anonymizes users with hiding IP address. Post installation, surfing dark web links will be an easy affair. Although competitors for Surfshark provide cheaper options, security is never to be treated as a second option.
BEST SEARCH ENGINES FOR DARK WEB LINKS

Dark web links has an alphanumeric style link naming pattern which makes it hard to remember website names. Therefore, it is a best practice to bookmark your links as soon as you find them. Another option is to use the updated search engines. Hidden wiki is the defacto standard when it comes to searching dark web. It has an indexing system which is the Wikipedia of dark web. Since a combination of numbers and letters won’t give anyone an idea, Hidden Wiki has shown the corresponding names as well. That is not all; there are informative pages as well in the weblink provided for Hidden Wiki. New users of dark web links should strictly adhere to safe standards and don’t browse farther from base Wiki index page.
BROWSING DARK WEB CONTENT

The world is fast paced and accelerating out of content. To meet the standards of demanding netizens, internet technologies have evolved. Much of the internet speeds have improvised during the past few years. New frameworks and evolved web development content has certainly boosted internet usage. However, there is a small community that still types their opinion on pale old html static pages. Dark web communities are thriving. With over many decades of internet address under its hood, dark web has been a tight competitor for many. Dark web relies on the TOR network for seamless operation. TOR or the Onion Router was a project developed and established for secret operations. During its glorious times, dark web was an enchanting mystery for users. The principle of maximum-security laid foundation during this time. Slowly, this internet freedom got misused. Now it has been a bane with chaotic marketplaces. Dark web markets are everywhere. They host illegal content and act as secure solutions for trading banned items. Journalists also benefit from dark web. This medium can be used to exhibit contents which are otherwise legally barred. Constitutional issues and local problems have been raised here in the dark markets of web. With strong foundation, dark web is a hard nut to crack. Several safe places as well as local regulations make it easier for hackers to spend their days in dark web.
ANONYMITY WITH DARK WEB
The name dark web has been synonymous with anonymity. Politicians, leaders and other categories of users have found shelter within it. Services of dark web vary accordingly. There are lots of activities to discover for new comers. But going deep into data markets can lead to activities that tarnish personal data. There are millions of ways in which users who are new to dark web can be spoiled. Right decisions at the right time can certainly save your data. Presently, data stored in huge servers are facing the wrath of dark hackers. Ransomwares and trojan packed software are illegally siphoning data. There is nothing that malware defenders can do about it. Due to the hosting outside surface web, it is hard to get details of ransomware software. Dark web hosting solutions are cheaper and provide anonymity for users. This has become a head ache for federal enforcement agencies. During the last few years, many websites allegedly selling banned goods were taken down.
DWINDLING FUTURE OF DARK WEB SITES

Many experts have criticized the existence of Tor in the present scenario. The situation won’t change for at least a decade. There has to be a monitoring mechanism to track down illicit websites. Several renowned security researchers have found out that when hackers access data, the same password can cause harm. In addition to brute force tactics, hackers of the new generation install remote scripts to try to log key data. As per their results, in some cases, a successful password could not be the best. The use of the same password for banking websites and online games is also very significant. The way data is distributed is one of the helpful characteristics of the dark web. Despite the architecture and connection stability of the 19th century raising many eyebrows, many lovingly enjoy TOR networks.
TOR BASICS: DARK WEB
TOR features relayed node configuration for data transfer. There are several machines with data journeys in between. It connects to relay nodes once the sender sends the information. Reports indicate that there have been security issues in the dark web for a quarter of the last few years. A research has been undertaken on Cyble, a private firm that conveys the status of government databases. They were hacked at the beginning of 2020 and personal information belonging to government agents was up for sale in markets related to dark web operations. Though dark web has become beneficial for users finding information that requires anonymity, there have been many cases of security breaches. Security threats that hinder people’s digital and financial security will create doubts in the minds of users.
UNDERSTANDING HIGHLIGHTS OF DARK WEB SITES

For security agencies, knowledge violation is a head ache. When it comes to surfing and web access, most organizations have stringent policies. Dark links to the web may not be available on the network. Even, that might not always be the case. An employee who inadvertently or deliberately accesses the dark web can carry with it a lot of problems. The effects can be painful once the network has been breached. To stabilize the network and put it back to shape may take over a year. To avoid mishaps, there are only a few things a network administrator should do. Getting a Plan B is one of the biggest checkpoints. There are no warnings when it comes to information infringement. It might seem that dark web links are harmless. The dynamic existence of TOR is due to the fact that the address must be updated regularly. A DDoS attempt will easily trace the attacker back when it fails. Therefore, regular changes of address are important. TOR networks are laboriously sluggish. Users will be wondering what happened to their link of 5 or 10 Mbit.
OLDER DARK WEB AND NEWER SURFACE WEB

Dark web links surfing is like a decade or so ago. The youth of today would be frustrated by the experience of browsing plain text html pages and page redirections that are not found. They have only encountered pages of eye candy java script loading at the blink of an eye. Safe browsing requires the customer upholding those principles. It could sound obscure that the dark web as a defense effect was initially flagged off. Yes, the TOR Project was a framework to shield the US Naval Research Laboratory’s private data from eavesdropping. Cyber criminals, on the other hand, have gladly chosen the dark web as a way of defending their criminal activities. Dark network connections retain anonymity, which is what a hacker wants. When time passes, the dark web becomes more malignant. There are several locations that sell illicit items on the market. Services are available in the dark web at your doorstep, including that of a hitman. Finding that child pornography has also become an option of interest is really troubling.
PRIVACY WOES IN DARK WEB
For security agencies, knowledge violation is a head ache. When it comes to surfing and web access, most organizations have comprehensive regulations. Dark links to the web may not be available in the system. Even, that might not always be the case. An employee who unintentionally or purposely accesses the dark web can carry with it a multitude of troubles. The consequences can be painful once the network has been breached. To stabilize the network and put it back to shape may take over a year. To avoid mishaps, there are only a few things a network administrator should do. The way data is distributed is one of the helpful characteristics of the dark web. Despite the architecture and connection stability of the 19th century raising many eyebrows, many lovingly enjoy TOR networks. TOR features relayed node configuration for data transfer. There are several machines with data journeys in between. It connects to relay nodes once the sender sends the information. The knowledge thought to be a relay that is automatically selected is taken by these nodes. This relay makes sure that the knowledge spreads around different continents. One of the highlights of the dark web is that, if you want it to be, personal data is secure. It is said so because the consumer has full control over details.
DARK WEB ALTERNATIVES

Getting a Plan B is one of the biggest checkpoints in accepting a technology like dark web. There are no warnings when it comes to information infringement. Within minutes, you will find that a fully operating device has broken down. The network admin team is responsible for handling it. Significant harm can be prevented once there is a plan B to backup necessary data and systems and to isolate the network entirely. Any network should therefore have a plan where they should expect a breach. A policy to track infringement and its implications should be in the planning. It becomes relatively easy to shape and track once a plan is set up. Another difficult duty is authenticating accounts. The two-step authentication ought to be used to identify users biometrically as well as individually. Two-step verification is a mandatory condition, much like Google downloading addresses. This helps users to regain their lost identities or alter passwords. Even, in cases of theft, this option can be used to recover or alter the password. This has to be accomplished through devices and platforms.
USER SECURITY WITH DARK WEB LINKS

Password reforms are necessary for banking forms, shopping apps, payment-based websites and other financially related sites. Life-saving authentication will be a second step later on. Monitoring credit card purchases is another free tip. Everybody now has a credit card. Not all the criminal activities reported in recent times had their parenting in the dark web. Security authorities report that Clearnet is also actively involved in recurring day-to-day crimes. There are many notable ways of the Dark web, one of which is the privacy factor. This offers supreme confidentiality. By installing an appropriate VPN package, users who access dark web links are advised to get an added layer of security. Installation of a specific browser package is required to browse dark web links. TOR is a popular browser which is a default component of TAILS, a Linux variant. For users, TOR provides a simple layout. One of the developed browsers available for the Dark web was TOR. It provides an interface that is similar to Firefox’s. TOR has been fantastic as an anonymous web browser and provides an excellent interface for first time users. It is compact and guarantees stability by providing reliable updates.
ACCESSORIES FOR DARK WEB

Waterfox is a light, reliable package that is built for the dark web. Installing and understanding it is simple. By not gathering any telemetry data, the package provides privacy. The latest edition of this browser also does not collect usage information. Also, this unique browser offers users extreme flexibility. Onion links mean a link to the TOR network that takes you to a dark page on the web. The pages need to be refreshed and the onion links are down most of the time. Using Tor2web is another way to access Onion Links without the installation of a browser. This service e is offered online. It helps users to call visible networks from dark web links, i.e. With Clearnet. However, it is highly recommended to do away with the practice of accessing tor links through a Clearnet browser due to the fact that Tor2web is not as safe as TOR installations. When such services are relied upon, the possibilities of a hacker accessing your personal data from the dark web are very high.
THE STRUCTURE OF DARK WEB
TOR’s relaying function provides a tunnel through which information can pass safely. Shielding your network links with a degree of protection is always a better option. The added layer of protection is provided by the VPN. When it comes to providing privacy, mobile devices are notorious for their unreliable services. Over the past few years, web surfing using mobile devices has been alarmingly endangered. In this sector, NordVPN is one of the most trusted VPN service providers in the industry. It has a particular smartphone suite as well. There are many other online VPN providers that, like the one mentioned above, offer powerful VPN services. For several decades now, privacy has been in your blood. Human rights activists have been on the scene for so long that, in recent decades, freedom of expression has made revolutionary improvements. This has helped to renew human rights principles and to recognize them as a constitutional right. This was confirmed by Article 12 of the UN Declaration of Human Rights (UDHR) in 1948. The mere navigation of dark network links will not deliver your home to law enforcers. However, the amount of doubt it throws will remain the same whether or not you enter an unconstitutional marketplace. In addition, the law enforcement agencies believe that there is nothing of interest in the dark web for law compliance.
TIPS AND TRICKS FOR BROWSING DARK WEB

The pure reason that the TOR network is run by dark websites allows users to use it without fear of being attacked by crawler bots. For their data exchange, government departments as well as journalists and whistleblowers rely on data repositories accessible on dark websites. The task of anonymous data exchange is unmeasurable in the present digital scenario. Using the anonymity provided by TOR, documents of tremendous importance are sometimes transferred. People are devoid of internet freedom in certain countries. For some reason, even emails are monitored. Even since the beginning, TOR’s increasing prominence has been substantiated by rough laws passed by different parliaments.
INVISIBLE CHAIN OF ACTIVITIES: DARK WEB

Digital crime is yet another face of criminality in the real world. The famed criminal justice writer Peter Grabosky in 2001 called this so. The same crime as human beings with weapons are committed by programs written or created using computers. In addition, the crimes committed using a machine only vary to a certain degree in the medium. Only the modus-operandi varies. As it’s a safe haven for them, dark web sites are often relied on by terrorists. A simple web page can be downloaded by agencies within a few months, if not weeks. The chances of monitoring the original poster are also very good. Enabling tor routing would mean that there will be a hard time for authorities. Financial loss is on the rise due to hacking attempts. Every day, new reports about hacking attempts and malicious code installation on servers are available. User accounts are being hacked and information is being leaked. Multiple personal profiles have been reported missing or updated, including those from social media websites. Cybersecurity reports by top corporations confirm that cyber threats rose in the first quarter of the previous year. On the dark web, malware and other malicious codes are readily accessible. These connections can easily be reached by users who have basic knowledge of dark websites and computers.
SECURITY THREATS WITH DARK WEB BROWSING

People are entirely responsible for detecting and profiling security threats emerging from dark markets. Not all of the Dark web websites are illegal. There are few that are as valuable as their obvious net counterparts. Intelligence sources, however, confirm that in the last decade the number of illicit trade hosts has doubled. Thus, it has become mandatory for a typical user to mitigate any malicious installations and evade certain trade markets. Our internet is a location where millions of networks have converged together. The availability of infrastructure is massive. To know about the dark web, a computer user does not need to be tech-savvy. Anyone who spends any time online may well have heard of this word. For others, it is enigmatic and some have never visited this dark area or made plans to visit it. The dreams highlighted by articles and weblinks made many interested in the dark web. If you are one of the interested users who would like to take a look at the deepest space of internet, then you may be helped by this post. Installing a TOR powered browser is one of the prerequisites. In earlier posts, the words TOR, dark web, and VPN were already detailed. For beginners, a brief introduction would certainly be of benefit. The Onion Router stands for TOR.
INDEXING IN WEB: DARK WEB LINKS

Indexing in dark web links can be described as an information retention register. Dark web sites can only be accessed by non-indexing methods as they are not accessible for indexing of these pages. During a user’s Internet hours, a search engine aims to gather as much information as possible. A search engine indexes it if a user is online and he is looking for something. Next time, the pages visited last time will be viewed in search when the user searches for similar items. With the support of crawlers, the way search engines do this is Crawlers are programs that allow items to be indexed by a search engine. Google indexing is now advanced and reliable. It is very complicated by the algorithms by which they do it. If a website is not indexed, the results would not reflect the details on the list. Thus, at the foot, it stays. The website can be accessed only by a user who provides the exact connection.
USER ACCESS TO DARK WEB LINKS
Just over 3 percent of the entire billion population accesses the Dark web links. It is operated by a small community of users and some of the websites are nearly outdated. Although the dark markets are reaping rewards, for many it is a daunting job at hand. Since it takes time and effort to manage servers and hardware, users generously contribute to the same thing. The role of managing social websites is often taken up by volunteers. The Dark web is fun if you’re ready to travel. It itself has a tiny hidden and personalized universe. Activities are everywhere. But beware of the black markets that are capable of captivating you. There are illicit drugs and other services offered there.
ISSUES AHEAD FOR DARK WEB
The purpose of this article is to expose the future of dark web sites. The view of many security researchers is that there is a low likelihood of a revival. Many of the websites have vanished already. Some are deprecated. User populations have shrunk and are finding it difficult to keep pace. In appearance, the Clearnet is more tempting. It also has content, pace and dependability. It is impossible for the tiny group of journalists or whistleblowers to manage such websites. The numbers as recorded from their downloads by the TOR project also indicate a decrease. The number of online and functional web pages has also fallen down to less than 4000. They are still under the scanner, even though market places are usable. Over the past decade, the popularity of the dark web has plummeted. Web page reliability has always been a problem. One of the TOR network’s early mail servers was Sigaint. Many users were annoyed by its low performance and heavy down time. The mail server also took several millions of mail correspondence that Dark web users had with it. After his final down time, Sigaint never got up again. Now, the sector has other reliable mail servers.
ANONYMITY AND DARK WEB: THE TWIN PARADOX
The primary reason why many resorted to Tor-based websites was anonymity. Redirect the dark web connections to services provided to its users. Some of the websites, however, reportedly collect information from users. In the dark web itself, they also sell it. Hackers and malicious code scripters are damaging others. A user’s tracking and his behavior are contradictory to the ideals of dark websites. Yet there are websites that want to steal data even though it is so. During one of its latest press meetings, TOR confirmed that the user’s base tor does not promote illegal activities. TOR enjoys a respectable culture that is reasonably secure with over four million users under the hood. TOR users enjoy a comfortable room in the dark spaces of the internet with different desires and good intentions. Even TOR has made an attempt to protect its network’s active services. A hard nut to crack is the avoidance of illegal events. But the user group will be able to keep the resources working to an extent through sustainable efforts.
SECURITY FOR USERS ACCESSING DARK WEB LINKS

The following tips are for you if you are an enthusiastic Windows user and sick of switching to other operating systems. It is safer to tighten the seatbelt for protection, as a user of an unknown domain. Your operating system (whatever version of Windows) is supposed to be modified and running perfectly. Users should also have a dedicated alternative with an active firewall, although the Windows version would be appropriate. Disk encryption is also recommended in order to deal with ransomware problems. Methodologies for disk encryption that are easy to understand are accessible on the Internet. In the dark web, certain of the most dangerous key loggers and phishers are functional. An established method of holding hackers at bay is to install an operating system like Linux. To a certain extent, VPN or Virtual Private Network also helps. It helps to hide real internet address during surfing dark web links. How can this be useful? Ok, on the internet, your IP address is your face. Hidden IP means you are not exposed anymore. In the same way, VPN functions. For beginner users, ExpressVPN is a stubborn choice. The ExpressVPN installation is a breeze. It works like a charm and does so at a low rate. It is also strongly recommended to allow a guest account when installing Windows. Delayed access to dark web connections is the only drawback to using a VPN.
REQUISITES FOR DARK WEB
A tor-enabled browser is the primary prerequisite for accessing the Dark web. It is only possible to access Dark web links by downloading such a browser. The market has a number of armed browsers out there. TOR browsers are similar in appearance to Firefox browsers. The installation is very easy and typically takes an average user about 3 to 5 minutes. It is best recommended to install any program connected to the dark web in a Windows guest account. If you are a Linux user, then the easiest and fastest way to go is by Paws. Digital Box is the best third-party software available for installation on a virtual machine. Installation of the program takes few minutes and once installed you can configure it for Linux operating system.
VIRTUALIZATION AND DARK WEB
A Tor browser running like a virtualized one in an isolated environment is comparably safer. This is not always the case, although enthusiasts say that the VM layer of the 5-layer onion protection is optional. Digital computers do not provide any options for safer surfing. VM exploits can be omitted if they are built in this way. But note that each and every protection layer helps to stay away from bad coders. Most advanced users advocate removing VPN services in order to reduce delays and improve flexibility. If you want to trade in the dark sector, then this is probably the way to go. Foolproof support is provided by VPN providers. A computer without VPN security is likely to be compromised in the case of an infection from the dark web. This will also show that their actual IP address will peel other layers of security away. If a VPN is enabled, human errors when accessing dark web links can be significantly reduced. As detailed in previous papers, our prescribed 5-layer protection offers improved security. Without worrying about phishing attempts, users can easily access dark web content. It should be noted, however, that any transaction made or an attempt to transact via credit/debit cards should be done very carefully.