
Not all websites provide the same layer of security. The invasion of websites into one’s private life has led to concepts like dark web. Dark web is an Internet network that is more or less private. Dark web is easily available in all platforms. It is simple to use and free, therefore it is dependable. Facebook has already implemented a TOR version. It is friendly, but not as efficient as clear net alternative. There are lots of servers running all over the world hosting dark web content. It can be accessible by downloading and installing software such as Tor, I2P, or Freenet, to name a few. Because all of this software is free, it is also free. To be honest, there isn’t a photo. It also aids in the prevention of sunburn. To access the darknet, you must be seated in front of a computer, which is still a significant advantage over the beach. When you’re on the darknet, you’re at home, alone, and preferably in a dark environment to avoid screen reflections. There will be no sunburn because there will be no sun.
WHAT TOR AND DARK WEB PROVIDES ITS USERS

You can watch everything on the internet, which is similar to the naturist beaches available all over the world. When you use the internet, your access provider has technical access to all of the data that travels unencrypted: the websites you visit, your Google searches, the comments you leave, the passwords you use on particular sites, and so on. The majority of darknets employ robust encryption techniques, allowing you to mask your identity from your ISP. When you utilize the dark web, you connect to a network of computers all over the world. When using Tor, for instance, you must pass through three computers before reaching your final destination. The first could be in France, while the second could be in Panama and the third in Australia. Have you ever been turned down for a reservation at a restaurant or a party? It will never happen again with darknet. A darknet’s core premise is to make all forms of content available to anyone. They are incredibly effective anti-censorship tools. Tor allows you to visit websites that are restricted on the internet. I2P, freenet, and Tor all allow users to host websites or data on their networks, making them essentially unblock able. You won’t be bothered by your neighbors on the dark web. The internet is worse than the French Riviera’s beaches. The number of Internet users worldwide is believed to be around five billion. Tor, by far the most popular darknet, with a daily user base of roughly two million people.
DARK WEB FOR LEGIT USERS

A very unusual type of Dark web writing exists: writing that appears for a few days and then vanishes, never to be seen again. Many Dark web sites are ephemeral, as I highlight throughout this book. They come and go in a couple of months. They frequently vanish for no apparent cause. They simply vanish off the internet, and because they were formed and maintained by anonymous individuals, there’s little prospect of contacting their former administrators to find out why they’ve vanished. Facebook is really the first Silicon Valley Company to officially endorse Tor as a network created to enable visitor’s access websites without tracking and broadcast their contents in search engines. According to Dr. Steven Murdoch of University College London, who was briefed by Facebook for the project, Facebook’s move would be popular among people who wanted to prohibit their location and browsing habits from being tracked. Users will still need to check in with their real names to access the site, he explained. The dark web sites work on TOR network empowers clients to utilize it unafraid of being attacked by crawler bots. Administrative offices just as writers and informants rely upon information entrances accessible in dark web for their information trade. In the present computerized situation, the part of unknown information trade is immense. Archives of tremendous worth are regularly moved utilizing secrecy offered by TOR. In certain nations, residents are without web opportunity. Indeed, even the sends are followed on purpose. Indeed, even since commencement, the developing fame of TOR has been validated by harsh laws authorized by different parliaments. Learn more about dark web links.
THE OPEN SPACE OF TOR FOR SOCIAL WEB

Virtual guiltiness is simply one more face of certifiable wrongdoing. This has been named so by the celebrated criminal equity essayist Peter Grabosky in 2001. Projects composed or created utilizing PCs play out similar wrongdoing as people with weapons. Likewise, to a degree, the wrongdoings carried out utilizing a PC simply differs in the medium. Just the usual way of doing things is changing. Dark web is additionally depended upon by fear mongers since it’s a place of refuge for them. A site free web will be brought somewhere near organizations inside couple of months if not weeks. Additionally, the shots at following the first banner are high. Empowering pinnacle directing will guarantee that specialists will struggle. Dim sites are open through dark web joins. They are regularly found in the catalogs, Reddit discussions and sheets. Activists, however ordinary clients mindful of protection likewise depend in TOR. An absence of engaging format hasn’t banished clients from getting to peak network joins. It is the usefulness of TOR that has overwhelmed clients. Deep web is considered as decent pollinated place for publicity stunts, enrollment and arranging. There are a few adventure markets where weaknesses are sold. Interruption of web frameworks was something no one but experts could bear.
GROWING TREND OF ANONYMITY PREFERENCE IN DARK WEB
Dark web is considered safe due to many factors that are laid out ion this article. But anonymity is of prime concern. Because of the ‘press me to hack’ method of programming advancement, even beginner clients are endeavoring to hack frameworks. This thusly leaves framework chairmen a run for their cash. Endeavors to take information or introduce ransomware program can seriously influence the standing of an organization. Arms dealing have likewise been a worst thing about the last decade. There is a site named as Euroarms where arms are exchanged. They convey merchandise to all pieces of Europe. Games, for example, betting is additionally well known in dark web. Monetary harm due to hacking endeavors has been on the ascent. Consistently, there are new stories on hack endeavors and establishment of malevolent code in workers. Client accounts are being undermined and there is spillage of information. Various individual profiles including that from web-based media sites have been accounted for lost or changed. Studies in network protection field by top firms affirm that there has been an expansion in digital dangers in the primary quarter of earlier year. Malwares and other noxious codes are effectively accessible in dark web. Clients who have straightforward information on dim sites and PCs can undoubtedly get to these connections. The product can be tried preceding establishment. With more than 95% of website pages still non-indexed, there is an enormous degree for malware producers to grow.
UNDERMINING TOR EXPLOITS: PRIVACY TO INFORMATION
The sole truth that secrecy is a quite a problem empowers them to do as such. Malware administrations have been on the ascent and as per information got from top security firms, the circumstance will proceed so. Conversations are on the ascent with shadow markets, for example, the Silk Road being undermined by FBI. Be that as it may, fresher groups are on the employ with much better security and administration. The entire obligation of recognizing and profiling security dangers arising out of dark web lies with the people. Not the entirety of the sites in dark web is unlawful. There are not many that are just about as helpful as their reasonable net partners. Nonetheless, knowledge source affirm that the quantity of illicit exchange has have twofold collapsed somewhat recently. Consequently, relieving any malignant establishments and sidestepping such exchange markets have gotten obligatory for an ordinary client. Our web is where different million organizations have combined. The foundation accessibility is huge. It has consistently been changing and there is still space for improvement. Concerning norms and innovation utilized, there is capacity to develop. The secret impact of dim sites has entranced numerous netizens into this profound world. Some website pages may imitate the properties of their Clearnet choices.
SOCIAL MEDIA IN DARK WEB

Clones are very prevalent in dark network. Such websites are legit and have enough security features to protect users. But there is an issue. Facebook for instance may have a cloned variant in obscurity web. Pinnacle has been at the center of attention for a long time now. It’s straightforward and allowed to utilize design has far reaching acclaim. It ought to be concurred that dark web come up short on the fabulousness of new gen clear net partners. Yet, with regards to proficiency, dark web can’t be set aback. The tor version of Facebook has issues when routing is enabled. This causes the website to raise alerts with regards to location of user. Regardless, of this point, many users access Facebook from Tor. Sites facilitating dull substance have been infamous among examination organizations. Thusly, the organizations in TOR address a plausible method for transportation of vindictive products. Regularly the great piece of dull net exercises is covered up by its terrible side. A client who can recognize and order the great and terrible will make some great memories making the most of its administrations. The need of detectable activities in uncommon dark web frameworks doesn’t basically pitiless they don’t exist. In actuality, in affirmation with the standard that rouses the dark web, the activities are essentially more irksome to spot and watch.
DARK WEB AND GENUINITY ISSUES
Heads inside the dark web are difficult to require a tall degree of covertness except if the outcomes, in case they are found, are satisfactorily genuine. It is possible that objections may come online at specific occasions, have a concise window of trading, by then disappear, making them harder to inspect. Aside from being unknown, dark web additionally help it utilized with secure association for move of documents. This article brings up the troubles looked during establishment and setting up of TOR for streaming dim web content. The twin sibling of Clearnet has a wide range of information available to be purchased. This is an upsetting reality that the 21st century is confronting. In any case, one ought to let it be known with no fault. Establishment of dark web requires compulsory arrangement of TOR empowered program. To peruse the pinnacle organization, one ought to have a viable program in their PC. Customary programs, for example, Chrome or Firefox won’t be satisfactory in this journey. Something else to note is that Wi-Fi network is consistently an issue with Linux and TOR when all is said in done. Additionally, since examination of substance sets aside time, web crawlers of dim net. So, on the off chance that you are experiencing a particular issue with Wi-Fi association, investigating the remote connector is required. The most obscure spaces of web enable customary netizens with protection. Be that as it may, it’s anything but a two-sided deal. On the other side, a similar dim web abuses security of others by sharing individual subtleties and private information on the web. Likewise, first time clients should take note of that there isn’t anything of interest in dim web.
ILLICIT SEARCHES IN DARK WEB

In the event that you are looking for illicit merchandise or media, at this point you are very much aware of the security requirements of TOR organizations. A PC client need not be technically knowledgeable to think about dark web. Any individual who has most likely invested some energy online may well have found out about this term. It is puzzling for most and some has even visited or made arrangements to visit this dim region. The dreams that articles and web links have featured made many keens on dark web. In the event that you are one among the intrigued clients who wish to bring a look into dim web, then, at that point this article may help you. One of the essentials is to introduce a TOR empowered program. The terms TOR, dim web and VPN has effectively been subtleties in before articles. A short presentation will certainly be of help for new comers. Peak represents the Onion Router. It’s anything but an unpredictable bundle that has a hub and layer related structure. Information heads out from start hub to end hub through a transfer. The hand-off keeps all information secure and mysterious. Thus, a client outside the organization can’t get to this information. Thus, dependability is saved. For simplicity of understanding, a hub mentions to any PC on the organization. Once a user gets in touch with dark web, it is easy to move on. Streaming content, downloading media etc. may take time and effort but there are much more bigger options out there. A one-time setup pain can be there for users. A Virtual Private Network or VPN has been a dedicated ally for protection concern netizens. It limits clients from the excruciating undertaking of hiding on the web personality.
VPNS FOR SECURE AND PEACEFUL BROWSING

SOCIAL NETWORKING THROUGH DARK WEB LINKS

PRESENCE OF PROHIBITED DARK WEB LINKS

Since the dull business sectors consistently centered on selling drugs and unlawful warez, programmers additionally focus on these offices. A few security organizations were additionally engaged with the investigation of profound boxes of the Internet otherwise known as dull web. To effectively evaluate these issues, an exhaustive comprehension of this maze of business sectors and destinations is required. It’s anything but consistently the dark web connects that is unlawful. This isn’t intended to be shared or sold illicitly. The term dull web has advanced from the worldview of Clearnet itself. It is incorporated into its anything but a wellbeing perspective. There is continually something to investigate, be it an ordinary client or a lifelong fanatic of the hidden world. In underground workers Black net hosts are accessible. In contrast with the tremendous Internet that we experience, the whole dark web network is 4% or less. So, for what reason are there such countless outrages available to be purchased? Indeed, in a real sense the dark web is gotten onion layers. The more layers, the more secure, it’s anything but an essential wellbeing related construction. A lot of dark net plan was expected to furnish its clients with security. In the conviction that all is good, security, safe-haven of information and trustworthiness, dull web joins give outrageous help.
DARK WEB LINKS: UNCOMPROMISED SECURITY

For establishment and admittance to pinnacle organizations, explicit programming is required. Allow us to investigate TOR or The Onion Router before what is dull web joins. The Onion Router is the foundation of a dark web or affectionately called TOR. It is really called the dark web itself. Peak is a specific program imparting stage. The hubs generally alluded to as clients are handed-off. These clients transport information from one hub as far as possible. In all manners this improves information insurance. Just the beneficiary approaches the information parcel and no other delegate approaches it. The absence of discernibility makes TOR select for the hard web fans. This brings opportunity of articulation inside itself. It has been over 20 years of fighting security barbarities. The dull web joins are not filed and accordingly can’t be followed via web indexes. This factor makes it hard to screen straightforwardness in the host content. Medications, weapons and burglarized information have gotten a top pick for wrongdoers in spaces of dull web joins. Since its initiation the Dark web has developed. In excess of 1,000,000 individuals overall financed and consistently utilized it. In the previous decade, innovative advancement has improved hugely. Comparative creation likewise has happened in obscurity web scene.
METHODOLOGIES TO SUSTAIN PRIVACY IN DARK WEB LINKS
The presentation of blockchain and progressed conventions for systems administration assisted with working with record partaking in dark web. Crypto-financial approach has raged the dull net. It was intended to decentralize cash use. Bitcoin and other exchanging plans immediately became hotly debated issues for tax criminals on the crypto area. The essential free net international associations have made rehashed fruitful endeavors to monitor their activities. Yet, when a market is bound, there will arise another market with expanded abilities. Political nonconformists are another class of dynamic activists who utilize dark web. Truth is told they get by in this profound space. Political nonconformists are another classification of campaigners who benefit intensely from dull web advancements. Additionally, with their beginnings recognizable to dull Web, occasions like Spring Arab have occurred. The Anonymous Greek word implies the covering up of one’s personality. The colossal number of computerized prints left by mankind treats, meetings and other innovative articulations is gigantic. Human portrayal is amazingly outrageous in the internet. Along these lines, advanced information is the main information organizations seek after. Pernicious makers of dark web endeavor to bait individuals into submitting bogus information. It’s worth great many millions in dollars. Clinical, individual and monetary data guarantees that associations screen a person. Yet, individuals don’t generally appreciate this.
DARK WEB LINKS FOR OPTIMAL SECURITY
Throughout the long term, the world has been overpowered by dark web. Little do organizers realize that data is followed both in web-based media and web crawlers? The start of COVID-19 unquestionably shook the world. Every one of the high-level economies has been influenced and many are arising out of it. In a few countries, the functioning methodology at home was tried and very much fused into the lifestyle. Radar dangers are additionally present to authorities on VPNs and restricted organizations. Organizations inside the monetary portfolio have upheld computerized reserves. However, our computerized warhorses have tried their flexibility against the dull web connections’ basic powers. Monetary elements need to consider the rising blast in dull web joins. It is fundamental to comprehend and address such issues appropriately on the dark market. In the commercial centers, monetary information is of extraordinary need. Crypto trades can be advantageously utilized by clients to arrive at a great large number of clients in a little compressed document. Likewise, high security organizations have been much cheered for the quiet transmission arrangement of the dark web. In relative terms, it takes under 5% of the web beneath its belt. Information security and data spillage was, in any case, an issue for residents. In any case, with far harder plans, new venders are creating.
SAFE BROWSING HABITS IN DARK WEB LINKS

The risk of malignant movement is additionally developing with extemporization in the meaning of work. Security establishments have additionally voiced an expansion in instances of infringement of protection and loss of individual property. Clients who need to remain in their house are utilizing dark web connections and web-based media to breathe easy. Nonetheless, attempting to impede such exercises is exorbitant. The design of the TOR networks is such that it postpones perusing speed. The public will see captivating things through an audit of exercises in dull web joins. Security scientists’ endeavors have really gone far in that regard. There were specialists who dissected the substance of the dull web joins following the conclusion of the infamous sites just as the Alpha Bay. Curiously, about portion of the dim ties was crushed spirit in 2016. It is possible that they had no material, or plainly the government specialists had brought down this site. Around 5,000 dim sites can be gotten to by means of dark web. Shockingly, a particular point is only 2000 of them up. Some are closed down irreversibly and others are not kept. It is essential to bring up those tricksters have two or three 400 potential places of section points of assault. That is threatening at this point. Because of their insight into clients of this dark web, focusing on them turns out to be simple. These incorporate secure elective drop boxes, Facebook substitutions and online media clones.
THE SCIENCE OF TOR: DARK WEB LINKS
The main thing that enters our psyches when we think about the dark web is detestable exercises. This is on the grounds that most connections can follow contemptuous demonstrations. The web for quite a while has been utilized to sell illegal meds, opiates, weapons and individual information. When a web association is down, a couple of more roots sprout from a similar fark net and it rehashes. The development of the dark business sectors can be followed to the protection based working climate drives of the US government. A web crawler isn’t accessible in web look on account of the inconceivability of ordering dull connections. For admittance to black market joins, either the catalogue or an immediate association should be utilized. At first, the Dark web was intended to help knowledge correspondences with a light on protection. The basic net partner has continually changed as per its necessities since its turn of events. It makes the TOR definition engaging. The TOR necessity was critical in light of the fact that significant administrative information should have been communicated. There was clear attempting to parody information, so organizations needed to pick peak organizations to send information safely. The meaning of the connections can be followed to TOR.
UNCOVERING DARK WEB LINKS
At first, TOR network was intended to get information move by the US Naval Research Laboratory. The undertaking was effective and was profoundly respected. It was regularly acknowledged as a free organization, and afterward became dark web. Peak is a push to keep clients unknown, as spread out by Radware, a main security programming organization. The achievement of dark web lies in its format. It exemplifies information sent through an organization. The information begins from the sender and is moved through a client channel. The information is gotten to by either the quick hub or the following hub in obscurity web joins. The lone data accessible is the last hub of the channel and the former hub. This guarantees that information transmission is unique and not channelled by any external parties.
DARK WEB LINKS AND PITFALLS

Despite the fact that the dark web appears to fledglings inventive and entertaining, prepared clients understand what lies behind these scenes. Illicit commercial centers are there on the dull web. The installment framework has been utilized subtly to advertise sexual entertainment and illegal items to youngsters. Because of its decentralized system, the approach of digital currencies has fuel exchanges. Today, in obscurity web joins are malware, individual information, card information taken and some different administrations. Ransomware has developed significantly and now gives buyers customized bundles. They are for unpracticed clients all way of malware, security encroachment applications and phishing bundles. The buying of such vindictive projects is a boycott for web clients, since straightforward working abilities are obligatory. The digital money blast has additionally expanded the development of clients in the mysterious organization. Dark web are unmistakable from the open net or more open web however comparable in highlights. As a profound web subset, the dark web and related dull web joins has a medium that is inaccessible to internet browsers. All in all, none of the standard programs utilized will give direct admittance to dull web joins.
USERBASE AND THREATS IN DARK WEB LINKS
Dark web entails a fortune for privacy concerns of users. The powerful assets of the dark web make it conceivable to cross the mysterious segments of the web. Peak networks are regularly utilized for criminal operations on the disadvantage. This supports what is viewed as a plentiful establishment of practically all the troubled human conduct that this world has at any point had. This doesn’t include controlled business sectors, character and abuse of individual data, data spillages, and so on Since the Silk Road was a famous illustration of why you ought not visit dull web joins before it falls in 2014. The Silk Road was a smooth space, as its name recommends, for opiates, weapons and other ill-conceived dealing. The FBI could require down its workers with praiseworthy exertion. It’s anything but an illustration of the Silk Road. In the haziest spaces of the web, there are a few thousand sites. They address humanity with all illicit or denied offices. Peak empowers obscurity on the opposite side of the coin. Its obscurity include empowers its follows to be managed. Effects had behind can be washed away rapidly. Dull web connections may add to the decision of TOR for a few associations and people. This is frequently alluded to as the mysterious web or the secret web; a little segment of the more profound web is regularly kept disguised. On the dull information base, web, sites and information are hard to situate because of explicit programming prerequisites.
WHAT IS IN DARK WEB LINKS: A PROMISING FUTURE

Dark web links are utilized to exchange firearms, and traded off charge card qualifications for untraceable product. In the event that the police know about somebody in the most obscure corners of the city to look, of the underworlds, so it is to be a recruited executioner, dealers, and pedophiles. As a result of Firefox, you, you can peruse the light web just as the profound web. In dull web connects your web traffic is all through the Tor organization, since every last bit of it is mysterious. When utilizing the Tor Browser, you ought to be mindful so as not to download it from any site other than the authority ones as this can present malware, spyware, or other infections to your PC or different gadgets. The authority line is that the Tor Browser is just deals with Windows, Mac, Android, and Linux. There are a few specialists who guarantee it is more secure to handicap outsider programs that utilization the Tor organization. Additionally, the dull web joins highlight delicate data and subtleties that can be seen without uncovering your character. These settings might be private workers, discussions, websites, or local area game conditions. Obscurity is the thing that makes the dim net so lovely. Nobody can sort out who is in reality one’s companions are, since, in such a case that they won’t uncover themselves, then, at that point you can’t realize who they’re out there. Columnists and informants additionally utilize the dark web connections and Tor administrations to secure their obscurity and protection, in addition to other things, which implies, in the trades of characterized data, like Snowden. It could be critical to take note of that the information taken from the Ashley Madison site was unloaded into the Tor organization. The uplifting news is that you can utilize Tor with either a VPN or through the underlying scaffolds (Tor hubs that are not freely listed). Particularly in the event that you are in the United States, a VPN will be a decent choice since it will be faster and safer. Just your ISP can see that you are connected to a VPN, while you’re utilizing Tor, yet a scrambled passage to a VPN implies that you can remain unknown and can’t be followed.
DARK WEB SITES: HOW DID THEY SPROUT
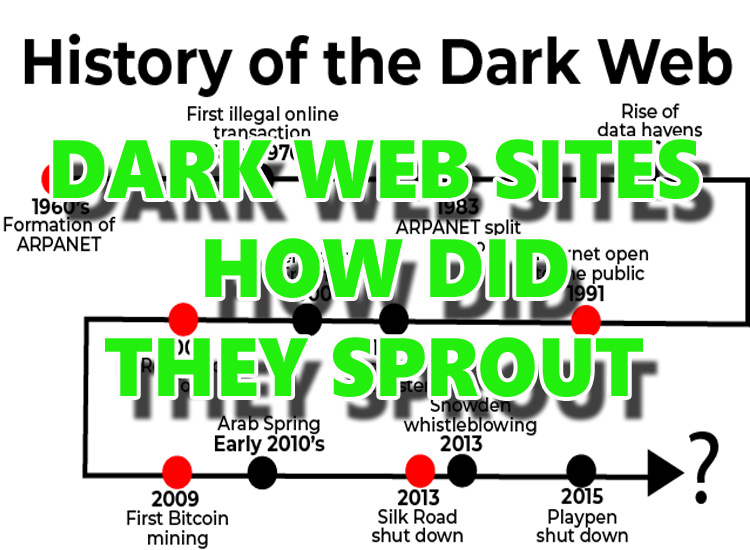
Dark net joins appear to be indistinguishable from each and every space on the Internet. Be that as it may, through nearer assessment, you will see unobtrusive differentiations, for example, name structure. Dark web sites finish in. onion rather than.com or.co. That is “the essential utilization of the high-level space addition assigning a dark mystery administration reachable through the Tor organization,” as per Wikipedia. Nonetheless, just programs outfitted with a reasonable intermediary worker are fit for getting to these darknet sites; a standard program can’t do as such. The second critical contrast is an obfuscated naming plans that outcome in hard to-recall URLs. Scammers make different darknet sites to hide their personalities. Additionally, online organizations that have been ready for action for quite a long time may become inaccessible if the proprietors wish to escape with the escrow supports hung in the interest of shoppers. Dark web sites have thrived because of the multiplication of bitcoin wallets. It empowers two gatherings to manage a believing exchange without remembering each other. While practically all dull sites acknowledge bitcoin or some other cryptographic money as installment, this doesn’t suggest that working together there is secure. For sure,
WHO ENJOYS DARK WEB SITES

Dark net joins exchanging stages have a significant part of similar attributes as customary internet business locales. This site incorporates standard highlights like evaluations/surveys, shopping baskets, and gatherings. Notwithstanding, another critical qualification between darknet business locales and customary trade destinations is the degree of value the board. Furthermore, that the two purchasers and dealers are unknown, each positioning framework’s standing is without a doubt sketchy. Appraisals on this sort of site are effectively contorted. Likewise, venders with a fair standing will suddenly disappear with their clients’ crypto-coins, just to return later under an alternate pseudonym. Most of web-based business specialist organizations have an escrow administration that shields the client’s assets before the item is dispatched. In any case, you don’t expect a consistent repayment measure during the debate. Since all contact on the dim organization is scrambled, even fundamental exchanges need a PGP key. Furthermore, the execution of an agreement doesn’t guarantee the conveyance of the items. Most of products bought from darknet sites may incorporate intersection worldwide boundaries. It is additionally reviewed by customs officials, who can hold onto unlawful bundles.
TOR DEPENDENCY IN DARK WEB SITES: DEFINING TOR BOUNDARIES
The dark net joins universe depends on the idea of complete obscurity. Subsequently, by making strides like utilizing a VPN, you can guarantee that the gadget can’t be recognized or followed. For other people, obscurity is a significant issue with regards to the Internet. They need to hold onto authority of individual information. Moreover, opportunity of articulation is a worry. Based on the main Amendment, others may advocate for mystery and obscurity. That is one motivation behind why honest residents regard Tor and other dim internet browsers’ protection. Secrecy may have valuable outcomes, like the capacity to share disputable yet real perspectives. Dark web sites are a subset of the web that must be seen by particular programming, for example, a TOR module, and isn’t straightforwardly available from the public web. Dim organization and darknet are likewise utilized conversely. All through this post, we will elude to the darknet as the organization foundation, for example, the TOR or I2P organizations, and dark net joins as the data that client’s interface and view.
MINDFULNESS WHILE USING DARK WEB SITES

There are a few fantastic sites that represent what dark net joins is, the means by which it became, and the vile conduct that occurs consistently there. This article would initially talk about secure access techniques, trailed by the various hunt choices accessible through openly accessible dark net search tools that slither dark web. Agents utilizing standard inquiry apparatuses on dark web sites should practice alert and be aware of the distinctions in outcomes introduced by various web indexes and even entertainers engaged with different types of darknets. It’s anything but prescribed to see TOR straightforwardly from a typical PC because of potential security outcomes. For a few groups, usability bests insurance, and they can associate straightforwardly from their standard workstation, yet this stance critical security concerns. Since the TOR program depends on Firefox, it is vulnerable to similar bugs as Firefox. While the Firefox group can fix messes with consistently, the overhaul can set aside some effort to hit the TOR bundle, presenting clients to chances. Given the intricacies of dark web sites connections’ material and webpage has, this can be a critical factor to try not to bargain your PC from an attribution or malware angle. It is encouraged to utilize secure connecting ways to deal with try not to bargain the attribution and host PC.
OPTIONS IN CONTRAST TO SAFE BROWSING VIA DARK WEB SITES

There are a few perspectives and techniques for accessing dark net joins. Coming up next is an essential guide laying out three decisions for associating with a dark web sites connect to have a more serious level of safety. Everybody has unmistakable passage obstructions, and clients can address connect in novel manners dependent on their requirements, financial plans, and different components. Dark web sites are slithered and ordered by an assortment of non-standard administrations, which implies that customary web search tools like Google and Bing can’t creep.onion pages on the TOR organization. Be that as it may, proxied TOR pages, which utilize TOR2WEB-type assets to permit clients to see dark net content by means of their typical straightforward internet browser, are regularly listed by Google, in spite of the fact that it’s anything but prescribed to get to these through an intermediary for attribution purposes. Web search tools frequently update or change .onion addresses. In the event that the entirety of the connections underneath is difficult to reach, or in case you’re looking for internet searcher URLs, a superior asset is https://onion.live/ – simply look for the web crawler’s name to get the URL. On the other hand, there are a few “covered up” wiki pages that contain an archive of instruments and dynamic web search tool URLs. The beneath is a testing of a portion of the accessible web indexes.
BOUNDARIES AFFECTING USAGE OF DARK WEB SITES
Secrecy is the essential explanation individuals visit dark net connects to utilize the legitimate programs. In spite of the fact that namelessness guarantees mystery, it additionally works with unlawful conduct. That is the reason dark web sites connections’ believability is discolored. The right to speak freely of discourse is certifiably not an all-inclusive event. Indeed, individuals everywhere on the world can’t put themselves out there openly because of unbending state strategy. Albeit agricultural nations vivaciously support free articulation, others can merely fantasize about it. The profound organization empowers occupants of these nations to articulate their thoughts unreservedly and unafraid of reprisal by law implementation specialists. Dark net joins empower anybody to bypass restriction and access any data unafraid. Also, dark web sites are a great discussion for doctors, researchers, researchers, and teachers to trade information openly and without oversight. Here you can get to data about logical tests that most of governments need to leave well enough alone. Furthermore, you may get data about wellbeing and social consideration that policymakers would prefer not to unveil.
BENEATH THE SHIELD OF DARK WEB SITES

Dark net connections may sound as unnerving as a blood and gore movie, yet it’s anything but a startling truth. The activity that happens there may detrimentally affect your riches or, more terrible, on your personality. It’s helpful to be careful and it shows that you’re set up to figure out how to shield yourself. Generally, dark web sites were planned to be a common workspace for specialists like government specialists and writers to team up on ordered ventures and offer select substance. All things considered, dark net joins are much of the time a shelter for hunters, psychological militants, and personality criminals. Dark net joins acquired its moniker by disguising checking subtleties, for example, IP locations and URLs, permitting all move to make place in the shadows. It’s a dull corner of the web where taken government backed retirement numbers are traded and sold with the end goal of fraud and misrepresentation. Dull sites can’t be looked or visited utilizing regular web crawlers or programs. Dull site URLs are secured by switch devices, which forbid web search tools and crawlers from ordering them. Moreover, this program stays away from reconnaissance, which makes dark net interfaces an optimal area for crime. Normally, the sites are utilized to give namelessness to guilty parties and nonconformists, to sell stash, and to get untouchable subtleties. Monetary organizations, as CFNA, and their partners frequently lead dark web sites searches to decide whether their establishments or customers have been hacked. A unique browser such as TOR helps to explore the dark web world. It works comparably to a standard internet browser however is much slower because of the numerous layers of encryption. To figure out how to explore dark web, you’ll likewise require a dark web sites index, like DuckDuckGo. DuckDuckGo is dark net interfaces client’s favored internet searcher and it is one of only a handful few motors that index. Onion areas – the space postfix utilized by all Tor web journals. Else, you would have the option to associate with sites just in the event that you know about their accurate location ahead of time. Remember that, since 2008, when everybody approached the Tor program, there has been a huge expansion in criminal behavior on dark web. This, specifically, has added to Tor’s and dark web sites connections’ awful picture. Utilizing dark net joins is likened to plunging with a tainted injury in shark-pervaded waters. Because of its uncontrolled presence, no one can tell what you will meet. Buying products is to a greater degree an act of pure trust than a guaranteed cash-for-administration contract – there are no terms of administration, and the merchant can’t be constrained to give you what you requested. There is a safer answer for access dark web. Introduce a VPN. Both urge you to see geo-confined substance which can be utilized to evade corporate or government oversight. Be that as it may, a VPN needn’t bother with you to look at a snail’s speed to keep up online security. Learn more about dark web links.
TWO-FOLD LAYER SECURITY FOR DARK WEB SITES – VPN CHOICE
NordVPN doesn’t request that you keep away from questionable substance to remain safe on the web. All that is vital is a membership. Also, NordVPN iOS application has a Dark web sites Monitor usefulness that tells you if your accreditations are settled. Peak (a protection network otherwise called The Onion Router) empowers clients to utilize encryption to get to the web from various passage focuses to data. Rather than having the solicitation of the web and information jump starting with one area then onto the next as regular switches do, Tor scatters the solicitation through a huge organization of transfers, to keep others from being in the know regarding the most recent data you have gotten to. As a rule, the archive, called a particle was, and still is, a stream outline that offers the capacity of inspecting the resulting phases of a handling, drawing the data/voyaging ‘particle’ away from a course over the long run, and in the end uncovers everything. At the point when you open the program window on your name and picture are promptly shown as a hyperlink in the visit window, making it hard to cover your personality from different clients when you peruse the web.
BROWSERS AND DARK WEB SITES

Dark web sites are accessible only through specialized browsers. TOR is a good example. Duck Duck Go search engine is also a favorable search engine. Administrative specialists utilize adequately able to sort out approach in this program, wouldn’t you say? Truth is told – it’s odd most definitely. Anybody should utilize the Tor Browser. To be exact, it is open source, free, usable for Microsoft Windows, Mac, and Linux PCs just as well as Android and iOS gadgets. In spite of the fact that it is actually the case that the device is generally far and wide, it’s hard to evaluate, on the grounds that no one has at any point tallied the specific number of clients. For the most part everyone, if they know it, utilizes the shallow Web each day. So, to guarantee that the kids you don’t open them to such repulsive encounters, get them far from dark net joins. Start by taking a gander at their PCs to check whether they are utilizing the ‘Peak’ (The Onion Router) first.
TIPS FOR PARENTS
Whether or not you are utilizing a PC, work area, or home PC, it ought to be not difficult to see whether the application is introduced for ‘Pinnacle’ is accessible on the framework. On the off chance that they were introducing programs, erase it and ask the youngster how they were doing the product and solicitation the arrival of any additional records they have made. Albeit ordinary programs will show you past search inquiries, you won’t see a hunt history in this specific one. In particular, it is essential to remember that dark web sites are intrinsically is an intriguing and fascinating climate. There’s an entire universe of enormous data covered up on the web that the kids don’t think about yet when kids start to learn.
KEEPING A CHECK IN DARK WEB SITES

Youngsters will without a doubt need to find something new and intriguing about this area. Along these lines, you may utilize a similar sort of rationale to portray an extremely profound, dark net regarding a profound, dim space, for instance although it seems like fun, there are numerous perils, like contamination, social alienation, and eventually being wiped out, no sane person will need their kid to take an interest in such a movement. An ever-increasing number of individuals are keen on dark net joins; it’s anything but a conspicuous topic of discussion. This can draw in the consideration of and interest of more and connect with the creative mind of more youngsters. To be in charge of our own lives, and put down certain boundaries is pivotal. You ought to know about innovation’s association on the off chance that you end up utilizing it. Basically, you need to have youngsters in your consideration to have the development and adapting abilities to manage these gadgets so they know exactly what they are, however you likewise should be set up to uncover the entirety of their dangers and make yourself available to them with the goal that they can get some information about their interests.
A BRIEF STARTER OF DARK WEB SITES

The web/surface net, which offers data and diversion to its clients, additionally has a clouded side. Grown-up diversion sites, discussions, talk rooms, explosives course, programmers, professional killers, illegal exploitation, and the bootleg market for firearms and opiates are largely instances of the clouded side of the web that are hidden behind secret web joins. This part of the web that represents a genuine danger to the worldwide digital local area and to worldwide security overall is a subset of dark web sites interfaces and is alluded to as the ‘dark web.’ The ‘dark net’ is a subset of dark web sites connect that commonly contains unlawful and against social data and can be gotten to through customary programs or concentrated programs for clandestine web joins. Because of the public authority organizations’ crackdown on dark web sites as of late, has moved to more clandestine areas. Dark net joins are a rewarding climate for wrongdoers and other enemy of social components since it gives them normal insurance from government offices. Also, the unaccounted-for tremendous economy of dark web sites is much the same as an expedition for distorted personalities. Also, the bootleg market for opiates, guns, produced distinguishing proof, human organs, and illegal exploitation all need an unknown area to work unafraid of government reconnaissance.