PRESENT SCENARIO AND DARK WEB LINKS
A broad description of dark web links, dark web sites and deep web links have been discussed here. The period of fear ware attacks came with the COVID medical emergency. These attacks are aimed at the aware clients who surf the web. Pandemic news continues to make headlines with relaxations across the globe. This is because of attacks of malware. The extent of malware available in dark web links cannot be traced easily. Studies conducted by leading security companies confirm that there has been a swarm of attacks. The sleeves have rolled out botnets and targeted malware. With VPN and other security measures available, the tech-savvy user always saves himself. However, what about ordinary network users; are they covered from the wrath of dark web links? This article is a deeper exploration of the dark web and its present condition and role in cybercrime. It is often construed that the root of malware events is the Dark Web links. That can’t be 100% sure. However, domains are compromised by dark web attacks. New users who are surfing dark web are more prone to attacks. Their personal identity is at a risk in the dark web markets.
PRESENCE OF ILLEGAL DARK WEB LINKS
Since the dark markets always focused on selling drugs and illicit warez, hackers also target these facilities. Several security companies were also involved in the inspection of deep boxes of the Internet aka dark web. In order to successfully assess these issues, a thorough understanding of this labyrinth of markets and sites is required. It is not always the dark web links that is illegal. This is not meant to be shared or sold illegally. The term dark web has evolved from the paradigm of Clearnet itself. It is built into its domain with a safety aspect. There is always something to explore, be it a normal user or a die-hard fan of the underworld. In underground servers Black net hosts are available. In comparison to the huge Internet that we experience, the entire dark web links network is 4% or less. So why are there so many atrocities for sale? Well, literally the dark web is secured onion layers. The more layers, the safer, it has an integral safety-related structure. A great deal of black net design was intended to provide its users with security. In the sense of security, privacy, sanctuary of data and integrity, dark web links provide extreme assistance.

DARK WEB LINKS: ACCESSING THE EASIEST WAY
For installation and access to tor networks, specific software is needed. Let us explore TOR or The Onion Router before what is dark web links. The Onion Router is the backbone of a dark web or lovingly called TOR. It is actually called the dark web itself. TOR is a specialized browser communicating platform. The nodes usually referred to as users are relayed. These users transport data from one node to the end. In all ways this enhances data protection. Only the recipient has access to the data packet and no other intermediary has access to it. The lack of traceability makes TOR exclusive for the hard web fans. This brings freedom of expression within itself. It has been more than 20 years of battling privacy atrocities. The dark web links are not indexed and therefore cannot be tracked by search engines. This factor makes it difficult to monitor transparency in the host content. Drugs, weapons and robbed data have become a favorite for offenders in spaces of dark web links. Since its inception the Dark Web has grown. More than a million people worldwide funded and regularly used it. In the past decade, technological development has improved tremendously. Similar creation also has occurred in the dark web scene.

NEWER METHODOLOGIES AND DARK WEB LINKS
The introduction of blockchain and advanced protocols for networking helped to facilitate file sharing in dark web links. Crypto-monetary advent has stormed the dark net. It was designed to decentralize currency use. Bitcoin and other alternating schemes quickly became hot topics for money launderers on the crypto sector. The fundamental free net International organizations have made repeated successful attempts to keep their operations under control. But once a market is handcuffed, there will emerge another market with increased capabilities. Political dissidents are another category of very active activists who use dark web links. In fact they survive in these deep spaces. Political protesters are another category of campaigners who profit heavily from dark web technologies. Also, with their origins traceable to dark Web, events like Spring Arab have taken place. The Anonymous Greek word means the hiding of one’s identity. The enormous quantity of digital prints left by humanity cookies, sessions and other technological expressions is enormous. Human representation is extremely extreme in cyberspace. Because of this, digital data are the most important data businesses pursue. Malicious creators of dark web links attempt to lure people into submitting false data. It’s worth thousands of millions in dollars. Medical, personal and financial information ensures that organizations monitor an individual. But people do not always enjoy this.

DARK WEB LINKS FOR ULTIMATE SECURITY
Over the years, the world has been overwhelmed by dark web links. Little do networkers know that information is tracked both in social media and search engines. The beginning of COVID-19 definitely shook the world. All the advanced economies have been affected and many are emerging from it. In several nations, the working approach at home was tested and well incorporated into the way of life. Radar threats are also present to officials on VPNs and limited networks. Companies within the financial portfolio have supported digital funds. But our digital warhorses have tested their resilience against the dark web links’ underlying forces. Financial entities need to consider the rising boom in dark web links. It is essential to understand and correct such problems properly on the obscure market. In the marketplaces, financial data is of great priority. Crypto exchanges can be conveniently used by users to reach thousands of thousands of users in a small zipped file. Also, high security companies have been quite applauded for the silent transmission system of the dark web links. In relative terms, it takes less than 5 percent of the internet below its belt. Data security and information leakage was, however, a problem for citizens. However, with far harder schemes, new sellers are developing. Learn more about dark web links.

SAFE BROWSING HABITS IN DARK WEB LINKS
The danger of malicious activity is also growing with improvisation in the definition of work. Security institutions have also voiced an increase in cases of violations of privacy and loss of personal property. This occurs soon after the beginning of the latest Coronavirus because of the public prohibition. Users who want to stay in their home are using dark web links and social media to pass time. However, trying to thwart such activities is costly. The architecture of the TOR networks is such that it delays browsing speed. The public will see fascinating things through a review of activities in dark web links. Security researchers’ attempts have actually gone a long way in that respect. There were researchers who analyzed the content of the dark web links following the closure of the notorious websites as well as the Alpha Bay. Interestingly, about half of the dark ties were broken back in 2016. Either they had no material, or clearly the federal authorities had taken down this website. Around 5,000 dark websites can be accessed via dark web links. Surprisingly, a specific point is just 2000 of them up. Some are shut down irreversibly and others are not kept. It is noteworthy to point out that scammers have only a few 400 possible points of entry points of attack. That’s menacing now. Due to their knowledge of users of these dark web links, targeting them becomes easy. These include secure alternative drop boxes, Facebook replacements and social media clones.

THE SCIENCE OF TOR: DARK WEB LINKS
The first thing that penetrates our minds when we think of the dark web links is nefarious activities. This is because most dark web links can track hateful acts. The internet for some time now has been used to sell illicit medicines, narcotics, weapons and personal data. Once a web connection is down, a few more roots sprout from the same dark web and it repeats. The growth of the obscure markets can be traced to the privacy-based operating environment initiatives of the US government. A search engine is not available in internet searches because of the impossibility of indexing dark links. For access to dark web links, either the directory or a direct connection must be used. Initially, the Dark Web was designed to support intelligence communications with a light on privacy. The simple net counterpart has constantly changed in accordance with its requirements since its development. It makes the TOR definition appealing. The TOR requirement was crucial because important governmental data needed to be transmitted. There was obvious trying to spoof data, so companies had to choose tor networks to send data securely. The definition of the dark web links can be traced to TOR.
TOR DEMYSTIFIED: – DARK WEB LINKS
TOR is the Onion Routing’s acronym. Initially, the project was designed to secure data transfer by the US Naval Research Laboratory. The project was successful and was highly regarded. It was commonly accepted as a free network, and then became dark web. TOR is an effort to keep users anonymous, as laid out by Radware, a leading security software company. The success of dark web links lies in its layout. It encapsulates data sent through a network. The data starts from the sender and is transported through a user channel. The data is accessed by either the immediate node or the next node in the dark web links. The only information available is the last node of the channel and the preceding node. This ensures that data transmission traces are not spread to suspected eyes. This improves data protection from prey eyes, allowing secure multilevel encryption. All this is free of charge, a TOR project initiative which has brought this up to its peak. Now, over a million users are going every day via the roads in the dark net. Users who prefer privacy rather than pace also visit TOR and take advantage of its reliable privileges.
BRIGHTER SIDE OF DARK WEB LINKS
Though the dark web links appears to beginners imaginative and humorous, seasoned users know what lies behind these scenes. Illegal marketplaces are there on the dark web. The payment system has been used secretly to market pornography and illicit products to children. Thanks to its decentralized mechanism, the advent of cryptocurrencies has fuel transactions. Today, in the dark web links are malware, personal data, card data stolen and some other services. Ransomware has grown profoundly and now provides consumers with personalized packages. They are for inexperienced users all manner of malware, privacy infringement applications and phishing packages. The purchasing of such malicious programs is a ban for internet users, because simple operating skills are mandatory. The cryptocurrency boom has also increased the movement of users in the secret network. Dark web links is distinct from the open net or more public internet but similar in features. As a deep web subset, the dark web and associated dark web links has a medium that is unavailable to web browsers. In other words, none of the mainstream browsers used will provide direct access to dark web links.

PRIVACY AND DARK WEB LINKS
Dark web links is a treasure for privacy-ushers as illustrated in previous posts. The robust resources of the dark web make it possible to cross the secret sections of the internet. TOR networks are often used for illegal activities on the downside. This nurtures what is regarded as an ample foundation of almost all the unhappy human behavior that this world has ever had. This does not involve controlled markets, identity and misuse of personal information, information leakages, etc. Since, the Silk Road was a popular example of why you should not visit dark web links before it collapses in 2014. The Silk Road was a smooth space, as its name suggests, for narcotics, weapons and other illegitimate trafficking. The FBI could take down its servers with exemplary effort. It’s just an example of the Silk Road. In the darkest areas of the internet, there are several thousand websites. They represent mankind with all illegal or prohibited facilities. TOR enables anonymity on the other side of the coin. Its anonymity feature enables its traces to be regulated. Footprints left behind can be washed away quickly. Dark web links may contribute to the choice of TOR for several organizations and individuals. This is often referred to as the secret internet or the hidden web; a small portion of the deeper web is often kept concealed. On the dark database, web, websites and data are difficult to locate due to specific software requirements.

WHAT IS IN DARK WEB LINKS
Dark web links is used to trade in guns, and compromised credit card credentials for untraceable merchandise. If the police are aware of someone in the darkest corners of the city to search, of the netherworlds, so it is to be a hired killers, traffickers, and paedophiles. Because of Firefox, you, you have the ability to browse the light web as well as the deep web. In dark web links your internet traffic is all through the Tor network, since all of it is anonymous. When using the Tor Browser, you should be careful not to download it from any website other than the official ones as this can introduce malware, spyware, or other viruses to your computer or other devices. The official line is that the Tor Browser is only works on Windows, Mac, Android, and Linux. There are several experts who claim it is safer to disable third-party browsers that use the Tor network. Moreover, the dark web links features sensitive information and details that can be viewed without having to reveal your identity. These venues may be private servers, forums, blogs, or community game environments. Anonymity is what makes the dark net so exquisite. No one has the ability to figure out who is in the real world one’s friends are, because if they aren’t going to reveal themselves, then you cannot know who they’re out there.

USES OF DARK WEB LINKS
Journalists and whistleblowers also use the dark web links and Tor services to protect their anonymity and privacy, among other things, which means, in the exchanges of classified information, such as Snowden. It may be important to note that the data stolen from the Ashley Madison website was dumped into the Tor network. The good news is, that you can make private use of Tor with either a VPN or by means of the built-in bridges (Tor nodes that are not publicly indexed). Especially if you are in the United States, a VPN will be a good option because it will be quicker and more secure. Only your ISP can see that you are linked to a VPN, while you’re using Tor, but an encrypted tunnel to a VPN means that you can stay anonymous and cannot be tracked.

THE ADVENT OF DARK WEB SITES
Dark web sites are available in plenty. There are several forums that host content on dark web sites. Not a day went by without internet users paying attention to the passage of time. This will require a thorough examination of all of the Clearnet web address as the connections to it will all be in depth, but, on dark web sites, there are still ties, right? Who cares about the “mysterious” businesses and activities in the “underworld” that don’t produce any direct profit or have a discernible goal? The essay looks at both how protected the dark web is and the level of protection you can expect when you use it, and compares it to how vulnerable people are when doing so people can see what they can be less comfortable with. In this part of the presentation, we’ll explore some basic concepts and concepts related to dark web sites, then switch to technical subjects like dark links. And the most part, people who know about the dark web, the majority of them disclose it publicly. Since this network contains a small, known quantity of risky factors, undesirables for women and children are a common concern, it disturbs them in different parts of the world. There are two blades to the broadsword; one to slash, and one to cut. Learn more about Dark Web Links: A Complete Guide For Beginners.

UNDERSTANDING AND ACESSING DARK WEB SITES
Start with one task, complete the task, go on to the next, expand and repeat, this procedure works well with dark web sites. These sites have loads of information that users can browse. There are untold tales about the forgotten areas of dark web sites. The simple truth is that it is yet another component of the internet. The general public is curious with it and where and where they will be able to navigate dark web sites. However, if you stick to certain simple safeguards, it is very safe. It is from these guidelines that the best guidance on how to surf the internet can be derived. For a more stable and healthy browsing experience, we ask that you stick to the guidelines mentioned below. By examining the Tor network, one can ascertain who and what the term ‘tor’ describes. The network is called a relayed one. This supports users in the process of inter-connecting nodes for data delivery. However, layering can be achieved at the user side, which allows for better control of the amount of damage. It is not overly difficult for new users to keep their surfing safe. When you are investigating the unknowns, the only caution is that the limits for protection of users must be strictly adhered to in our writings; we should not want to get around the fact that compliance authorities are well known as being prevalent in using dark web sites.

PRIVACY AND DARK WEB SITES
You have your own protection and privacy to think about. Note that the fact that these connections could not be real, they should be thought of as links, hence understanding the value of a connection should be kept in mind when traversing the dark web. The difference between the web and dark web sites is that on the web the content is readable, but on the dark web the destination address is hard to find.
In order as not to switch between different operating systems when switching between operating systems, you will enjoy these recommendations for Windows lovers. Since it is assumed that the subject does not use a particular domain, the seatbelt should be used to secure it. As long as you keep the operating system current, it is believed that it will be operating correctly and effectively. The firewall should be applied as an additional control to those settings, as well as to Windows XP’s automatic configuration; however, it is not required if the basic one is allowed. The need to defend against ransomware an attack is also necessitates the implementation of disc encryption. A simpler way to grasp methods of disc encryption is now on the internet. Eighty percent of unsafe keyloggers and eighty percent of scammer envois operate in the deep web.

SAFELY USING DARK WEB SITES
Security of life and property is of paramount importance in dark web sites. Therefore, as a concerned person, you should have revised encryption keys and 0-day change detection policies. Windows users are targeted by script writers over and again. In addition to creating a standard user or machine visitor account, you are creating an optional account where another part of your PC is protected from unauthorized attempts. Taken together, they are both windows-oriented hints, so users can adhere to them. It’s not uncommon for the loss of important information and data to occur as a result of carelessness. The lack of uniformity has enabled eavesdroppers and hackers to target this system as a target has become the goal of surveillance and cyber warfare. One of the best ways to avoid security risks when browsing the dark web sites is to search thoroughly. After almost ten years ago, VPNs have been considered to be the most important tool for online privacy and security. They’ve camouflaged several Internet Protocol addresses in order to cloak illegal acts in dark web sites. Right from accessing a bogus site to completing a fraud transaction required a tried party monitoring. This is made available with the help of VPN and IP covering tools.

VIRTUALIZING USING DARK WEB SITES
The security benefits of virtual machines have been steadily increasing. VPNs have proved to be a success in accessing dark web sites. Accessing black markets using TOR networks have been on the rise. Users are secure in VPN coupled networks. The installation is pretty simple. By far, the safest way is to incorporate accounts that can be limited as a single-use visitor. People do not use the built-in administrator account for accessing websites that are on dark web sites. An account like Gmail that is open to everyone is nice to use from time to time. The only protected approach is to make sure your identity is not be breached. After all, everybody is against the chance of getting their credit cards stolen, who wants to risk that. The anonymity offered by a virtual private network (VPN) while performing web searches in the dark web sites. Linux as an operating system is seen to keep hackers out of your system is a reality. It also supports to some degree via a VPN (or virtual private network) this tool stops you from unintentionally clicking on actual internet links when doing research in the dark web while claiming to be on the dark web sites. What good is this to you? As a matter of fact, your IP address is your face to the world.

VPN AND DARK WEB SITES
You are no longer exposed if the IP is hidden as it operates in the same way. Security is a service that is not recommended for those who only want to test the waters and learn about VPNs. The installation of ExpressVPN is simple and fast. In fact, it protects users from malicious dark web sites. It has a remarkably strong function, minimal impact on the bank balance sheet, costing little or none in increased expense. When people want to add Windows on a guest account, allowing the guest account also increases their security. The primary disadvantage of using a VPN is that there would be a short wait when trying to navigate dark web sites. This is due to the fact that the dark web sites are much slower and shaggier than the standard internet via multiple nodes. The time required to Travers a node is greatly increased. VPNs make the situation worse. In order to improve the accuracy and correctness of the calculation, users should go on the defined channel. It is strongly advised to use a VPN you can trust. You should still ask the service provider for another option if you have any problems.

MAIL ACCOUNTS IN DARK WEB SITES
The clients who use personal mail on the dark network can be called foolhardy if they are given the benefit of the doubt. There is no guarantee of being able to be protected from it even though you stay concealed in the dark network. Many of the dark web connections are a security threat to your privacy. No one can say for sure what lies under each one of their hats. The dark web sites can be unsafe to use for multiple identities, since a lot of dangerous criminal services are found on it, and you should still use a different identity for dark web sites. This will serve as a new Gmail id for you to you. This class of anonymous web services like Proton Mail, for example, also contains advanced features that allow users to host sites with fully obscured IP addresses. Users will get extra hosting facilities at Privacy.com for the development of anonymous e-sought email accounts. In addition to this, a client can only be built into the user’s account’s account. The object of this command is to protect your key account. After the app is set up, the instructions tell you to open the client and make sure that it works. The settings are extremely basic; all you have to do is add them. No previous scientific knowledge is needed. An exit node is where the service (and its communication) will be located in the future is still knowable. It is known to other nodes on the network. There’s no way that this could happen outside of your home world. After being mounted and configured, the VPN doesn’t need any further focus.

DARK WEB SITES AND THEIR PATH TO USER COMMUNITY
Long before Clearnet had lost the fight, dark web sites and connections continued to spread across the internet. Almost every type of contraband is for sale on these markets. To the government’s disappointment, every now and then they have to start lowering the boom on economies that were booming in the dark web sites. But newer ones will open up while the existing ones are filled in. The never-ending fight between authorities and dark web agents is a trauma for public. For all interested users all over the world, guns, ammo, medication, and drugs are available here. The method is simply registering your e-mail and signing into your account at either of Amazon or Newegg. It is important that those who are interested in using the dark web sites in a secure manner adhere to the rules. This is because there is a high possibility of undesirable content being present. An alternate path, regardless of its outcome, is highly detrimental to your personal well-being and to property. This article has explained the safety precautions you should take while swimming in dark web sites.

WALKTHROUGH ON DARK WEB SITES
The term dark web sites are typically referring to parts of the internet which are very secret and encrypted. To gain access to the complete or advanced level of the dark web, the use of a Tor browser is mandatory. There are only browser add-ons that allow you to enter the dark web, unless you install browser extensions. There are many possible customers who could purchase an armed version of this browser. Firefox and Chrome browsers appear to be the same to a certain extent. It typically takes around 3 to 5 minutes for new users to get their first experience of WordPress 3 up and running, on average. Dark web sites applications can be accessed by a Windows user account as a visitor, or as it won’t work properly if installed to the standard user account. If you are a Linux user, then you can use Tails for best and much of your Internet browsing privacy. Virtual Box is the most widely-used third-party virtualization platform for building and running a virtual machine. When you will run the installation program for Linux operating systems, it will only take a few minutes to complete, and then you can personalize it. Dark web sites are also available through forum links such as Reddit and Pastebin.

CONFIGURING COMPUTERS FOR DARK WEB SITES
When you click on a link in the dark web sites, a connection is made to the Tor network. This web connection works much like a regular net-based link, taking you to a website that is located in the dark net. Check to make sure your VPN is operational here. If you want to use the same service from your guest account, make sure your VPN is operational first. Any of the operation inside a virtual computer can be resettable, in the future. The host user must log into the guest account after Windows has begun to finish setting up. If the link is created, you can quickly enable the virtual network gateway and then connect to the installed virtual machine. The only condition is that you must be able to reach the Linux virtual machine’s console from within the host OS. Therefore, following these protection guidelines will allow you to defend your machine from malicious dark web sites. The guest account or surfer account can only be used for accessing dark web. People should avoid using it for anything that’s not of vital importance. A note of caution: Netizens should be careful when searching dark web sites as they must not to avoid entering personally identifiable details. We must use a name that does not identify who we are, and a password that is distinct from ours. So, whether you are using a VPN or a virtual machine does not make any difference, as long as you share your name. The resources are ready to protect a person from unnecessary harm when they’re surfing the web.

VPN AND DARK WEB SITES
If you don’t want to go to the trouble of configuring a VPN and downloading a virtual machine, this article is not for you. Advanced users of dark web sites typically find daily topics on dark web protection dull. Several different security options are discussed to ensure that users are protected in dark web sites are protected here using VPN. The virtual world has an equivalent or superior level of protection, to that of safety in a tor browser. Some say that the VM 5-layer onion router is merely being a vanity layer, while others contend that it is an integral component of security. Any approaches for more secure browsing do not deliver virtual machines. Exploits for Virtual Machine (VM) installations may be omitted this way. However, it is important to remember that each and every level of protection helps to prevent coders from entering. On the whole, experienced users find VPN unnecessary. The vast majority of users would choose more stability over less delay. You may want to do business in dark web sites but in this case, you may turn a profit by creating chaos. A trustworthy VPN provider offers impenetrable assistance. In the event of an infection from dark web sites, A computer without VPN security is likely to be infected. [These individuals’ true Internet Protocol addresses would therefore reveal] all the previous levels of security.

DEEP WEB CONTENTS
The definition of the “invisible web” or deep web varies from that a search engine. Search engines can find information on sites like Investopedia, which is part of the surface web. Deep web links are, according to most researchers, much larger than the surface web. The deep web is a mysterious and dangerous place. This is the part of the internet that is not revealed to the rest of the world. Deep web links is enigmatic, anonymous, and incredibly hazardous. The abovementioned site is closed off from the rest of the web for security reasons. There are over a hundred trillion websites on the internet, but just a fraction of them is linked to the “by means of search engines”, which are thought to be located on the “on the surface network”. This is an example of the vast amounts of material on the internet that are hidden and unattainable by standard search engines. The fact that there are millions of websites on the deep web never fails to amaze people. The first time you go down the rabbit hole, you can find many different things to read on the internet on the topic of the deep web, thousands of papers and other documents appear. Additionally, there are some things that you do not already know about deep web links. There are approximately 500 billion archives on the deep web links, as well as web connections that are located on the Dark Web and completely concealed from internet users, the general population.

DEEP WEB LINKS: CLASSIFICATION AND TECHNICAL EXPLANATION
Many webpages are dynamically generated or do not contain external deep web links. The search engines can’t locate them because they have connections from previously indexed pages. As a result, obtaining deep web links from other websites is a fundamental concept in search engine optimization (SEO). Another significant source of deep web content is fee-for-service websites. While fee-for-service websites like Netflix are accessible via the internet, the majority of their content is not. To access most of the material provided by these sites, consumers must pay a fee, create a user id, and create a password. Deep web links content is only available to those who are willing and able to pay the fees. This restriction of knowledge to paying customers runs counter to the early Internet’s egalitarian spirit. Although movie rentals can seem negligible, serious analysis tools such as JSTOR and Statista charge fees. The deep web also relies heavily on private databases. Private databases can be as easy as a Dropbox folder with a few photos shared by friends. Financial transactions made on big platforms such as PayPal are also included. The most important aspect of deep web links is that they enable people to exchange or save information without having to share it with others. and the portion of the Site hidden from ordinary view (i.e.by. never retrieved by search engines) For final clarity, the ‘dark web’ pages are part of the ‘deeper’ parts of the internet. The deep web links are renowned for being the most associated with the Silk Path. Laws have been created that allow mainstream search engines to index specialized for the dark web, but it is difficult to access many of the darker websites.
DEEP WEB LINKS DEMYSTIFIED
95% of the deep web links content is made up of open-source content, but half of the deeper material is found in copyrighted databases. The vast majority of all words that confuse people are associated with the terms “deep web” and “dark web”. However, these are two words that are used in the same manner. In certain ways, the dark net is a small portion of the larger network, and in some ways, it’s all of it. illegal trade is the side of the internet which takes place in the deep web links, where goods, such as guns and pornography, are sold. The so-called illegal activities will let you access to the depth of knowledge you need by doing this. There are important differences between the deep web and other types of websites. One of these is that the ones on the deep web are very difficult to find unless you know where to look. The “dark net” or “hidden web” portion of the internet is described as an extension of the TOR project, therefore, that contains files which are specifically encrypted, making them more difficult to view using traditional software. To have a special browser and need a very deep IP address to connect.
TOR AND DEEP WEB LINKS
Deep web links offers ample anonymity and also secures the device. The TOR browser is needed to scan the deep web It simplifies shopping online. you can pay using virtual money such as Bitcoin The choice to purchase or sell something anywhere, no matter what the currency is has been a big advantage of deep web links. It is best to stop the use of credit and debit cards when making online transactions since the link is unsecure. The deep web is a large body of web content. Some of the stuff may amaze you, while others terrify you. You might encounter odd facts or find yourself totally irritated. Because all the facts might not be right, it is important to note that you just trust half of deep web links. Any of the information can be distressing, so stay away from such troubling websites or locations on deep web links. One of the fascinating things about the deep web is that you can buy virtually everything anywhere. However, you can purchase hard drugs or contraband on the dark web. This seems to be very questionable behaviour and hence may have raised a lot of alarms on the deep web.
MALICIOUS FACE OF DEEP WEB LINKS
Serious illegal activities on deep web links will get you into legal difficulties. There are not many people who have card information for virtual currencies, so you should not look into those details. Many suspect that the US government has a substantial influence on the dark web. Different sources assert that the anonymous websites and other intelligence sources play significant roles in financing deep web links. A total of 1.2 million dollars has been spent on this initiative. Deep web links can protect your identity while entering the deep web. If you go on deep web so your identity will be compromised as well. The following are some of the significant features of the Deep Web. The truth can be quite fascinating to some people and quite troubling to others. Be confident you have reviewed all the facts and concentrate on the relevant information. If you proceed with caution, you can glean information from the odd parts, but you should still keep an eye out for oddities. These details can be important because accessing the deep web can be handled and bound properly. The deep web links is any website that cannot be easily found using a traditional search engine such as Google. This is due to the fact that the article has not been indexed by the search engine in question.
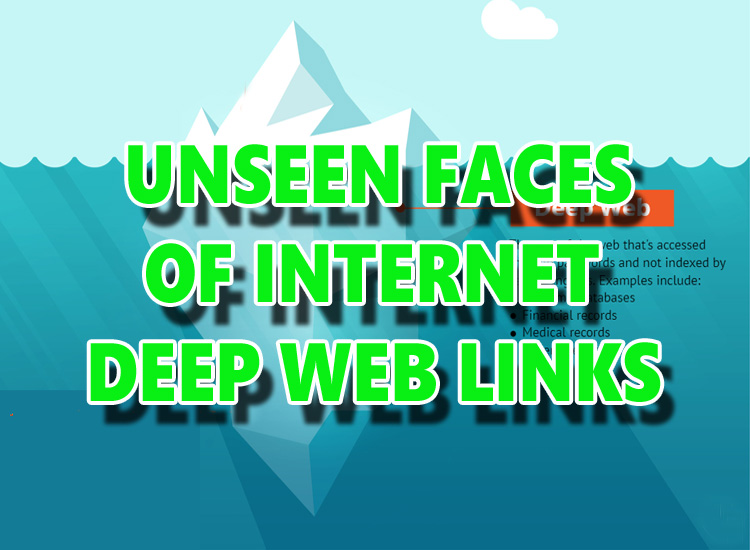
UNSEEN FACES OF INTERNET: DEEP WEB LINKS
The Deep Web is just another “step” of the internet, in layman’s words. It is the internet’s lowest floor, located under the “surface.” Indexing is best demonstrated by the modern search engine Google and its robust, high-performance indexing system. Google’s indexing methods depend heavily on a mechanism known as “creeping,” which is analogous to a virtual spider crawling through the multitude of pages on a website that can be reached via clicked links. A cursory scan is done, translating the content of the pages to a recognizable format. It’s then sent to Google’s huge index servers, where the data is entered into the search engine’s algorithms. If a website is not indexed by a search engine, it can only be reached by following a path to the URL or entering the same web address into a web browser. The potential of deep web links to facilitate private use and contact benefits a wide variety of users. Individuals or organizations that have benefited from the Deep Web in the past and continue to benefit from its presence are listed below. Anonymity is critical for these figures, who use the deep web links as a tool to perform contact initiatives in a secure and confidential manner.
USES OF DEEP WEB LINKS
Former military, administration, and business workers are banding together to report pervasive (and previously unknown) misconduct in their sectors. Working alongside investigative reporters, these people may communicate top-secret and sensitive information to the public in order to uncover wrongdoing while maintaining a level of confidentiality. People living in authoritarian regime-ruled countries often lack convenient access to news, media, and vital data pertaining to the health and survival of society as a whole. deep web links provides members of society living under authoritarian political regimes with a comparatively secure way to obtain critical knowledge for their own needs, as well as export it out of the region. The deep web links secret world contains a wealth of data, facts, and possibilities, including but not limited to the following. Because of the stealthy existence of many areas of deep web links, it is difficult to know how many deep web sites exist at any given time or to have a detailed image of everything in it. “No one can tell with certainty that they have thoroughly reached its depths,” according to the study. It is also a constantly evolving environment due to the arrival and exit of new services and marketplaces. Many people use it to purchase drugs and other illicit products from ostensibly untraceable websites. People who “seek to stay anonymous or set up pages that can’t be tracked back to a real location or person” often use it.

SECURE INTERNET WITH DEEP WEB LINKS
People who wish to shield their privacy and correspondence from state and private monitoring, such as informants and journalists, are included. According to deep web links, “dissidents in repressive regimes can need anonymity in order to securely inform the world about what is happening in their nation.” The internet has permanently altered human life. It influenced our classes, families, relationships, and workplaces. Indeed, there are workers and whole sectors that are purely dependent on the internet. Schools are using the internet to extend their horizons more than ever before. They are engaging with other schools all around the world, using foreign opportunities, playing new sports, and many more. While these are tremendous advantages, deep web links still raise enormous challenges. One of the most serious issues is what could happen if children have access to the deep web links.
A SKIMMED GUIDE ON DEEP WEB LINKS
The vast majority of what we know about deep web links.is that it is evil, scary, and harmful. We obviously want to steer our children safe from this. So, what if they are curious? What if a friend leads them to one of the many horror games available on the dark web? What if they mistakenly run across anything they shouldn’t? All you need to know about deep web links, deep web, and Tor Browser is given below. The deep net includes something that needs a password, such as databases or personal records. Since these pages aren’t indexed, they won’t appear in a search engine. You can’t use Google to find your personal bank account. You can only enter the main banking page and log in from there. deep web links.is all that exists beyond the username. The deep web is also a place for journalists and whistle-blowers to freely share classified details. The dark web, also known as the black web, is the “unsavory” portion of the deep web. Since most sites create an encrypted connection and disguise IP addresses, access to the dark web is only available by specialized browsers such as Torte dark web does not have anything that is illegal. The dark web has a huge reader population, but the content will range from the Invisible Man to The Anarchist Cookbook. However, there are many black markets on the dark web, the biggest of which is The Silk Path, which was shut down by authorities after the arrest of founder Ross Ulbricht in 2013. What really is the Deep Web?

WHY DO WEBSITES MAKE USE OF THE DEEP WEB?
Deep web links essentially refers to internet sites that are not indexed by search engines. In other words, you won’t be able to identify them if you use a search engine like Google. This ensures that you must know the precise address of the site in order to use it. While within the deep web links, the only other way to enter a deep web site is to click on a link. Internal pages of businesses, organizations, and colleges are used in the deep web. In addition to personal accounts for banking, email, and other services, the deep web can include online databases and password-protected pages. Many customized and password-protected pages appear on the deep web because they contain information that cannot be made public. Both deep web links and dark web links share one thing in common: their material is not meant for general use. The copyright owners may go to considerable lengths to make the information unavailable by ensuring that it does not appear in internet browser search results. It is worth noting that deep web links is not necessarily illegal, and there are also things taking place that are completely legitimate. Activities like those mentioned below are prevalent on the Deep Web, with membership often made up of well-versed internet users who know how to navigate deep web links.
DEEP WEB LINKS VS DARK WEB LINKS
The deep web links and dark web links have been mixed together in the popular imagination most people are unaware that the Deep Web includes blogs, such as the paid membership pages, such as Spotify, and password-protected email don’ What if anyone else only had access to your personal email inboxes by just typing your name into a search engine and pressing enter! also, the Deep Web is huge: back in 2001, was thought to be up to four or five times larger than the Surface Web; it has continued to expand exponentially since then. By contrast, the Dark Web consists of only of thousands of pages. The Tor sites are known for their use of encryption software that is intended to make users and locations anonymous. and it’s for this reason that illicit activity occurs on the Dark Web so people can withhold their identities, websites can be hidden, and personal data can be transmitted anonymously. Therefore, the Dark Web is a hotbed of illicit drug and gun sales, pornography, and gambling. The FBI ended an infamous internet black market on the Silk Road in 2013. But it’s not totally black. Additionally, it is used by whistle-blowers, whistle-blowers, and journalists who may be targeted by their governments. most notably, one notable exception to this rule is the website WikiLeaks, which is located on the Deep Web.
